M-Trends 2026: What 450,000 Hours of Incident Response Tells Us
Exploitation is the dominant attack vector, dwell time gains are reversing, and the application layer remains problematic
Google’s Mandiant recently released M-Trends 2026, their annual deep dive into the threat landscape built on frontline incident response data. It is one of the most respected reports in the industry and one I cover every year because it doesn’t rely on surveys or self-reported data.
It is built on what Mandiant’s consultants actually see when they respond to breaches. That distinction matters because it separates signal from noise in an industry drowning in both, and makes it one of the more valuable reports I look forward to each year.
This year’s report covers data from over 450,000 hours of incident response engagements across 2025. It spans campaigns, threat actors, exploitation trends, and sector-specific targeting data. There is a lot in it, but as I do each year, I want to focus on what this report tells us about the state of application security, vulnerability exploitation, and incident trends, and this year, there are some critical threads tied to AI and agentic systems that are impossible to ignore.
I have written extensively about the exploitation problem over the past year. In “Vulnerability Velocity and Exploitation Enigma’s,” I broke down the acceleration of exploitation timelines and the collapse of the window between disclosure and weaponization. In “The DBIR is Entering its Vulnerability Era,” I covered the Verizon DBIR’s confirmation that vulnerability exploitation had tripled year over year. In “Context is King but Prioritization is Priceless,” I highlighted how 98% of vulnerability findings are noise that buries teams in toil without reducing real risk. M-Trends 2026 reinforces every single one of those themes and adds new data that makes the picture even more urgent.
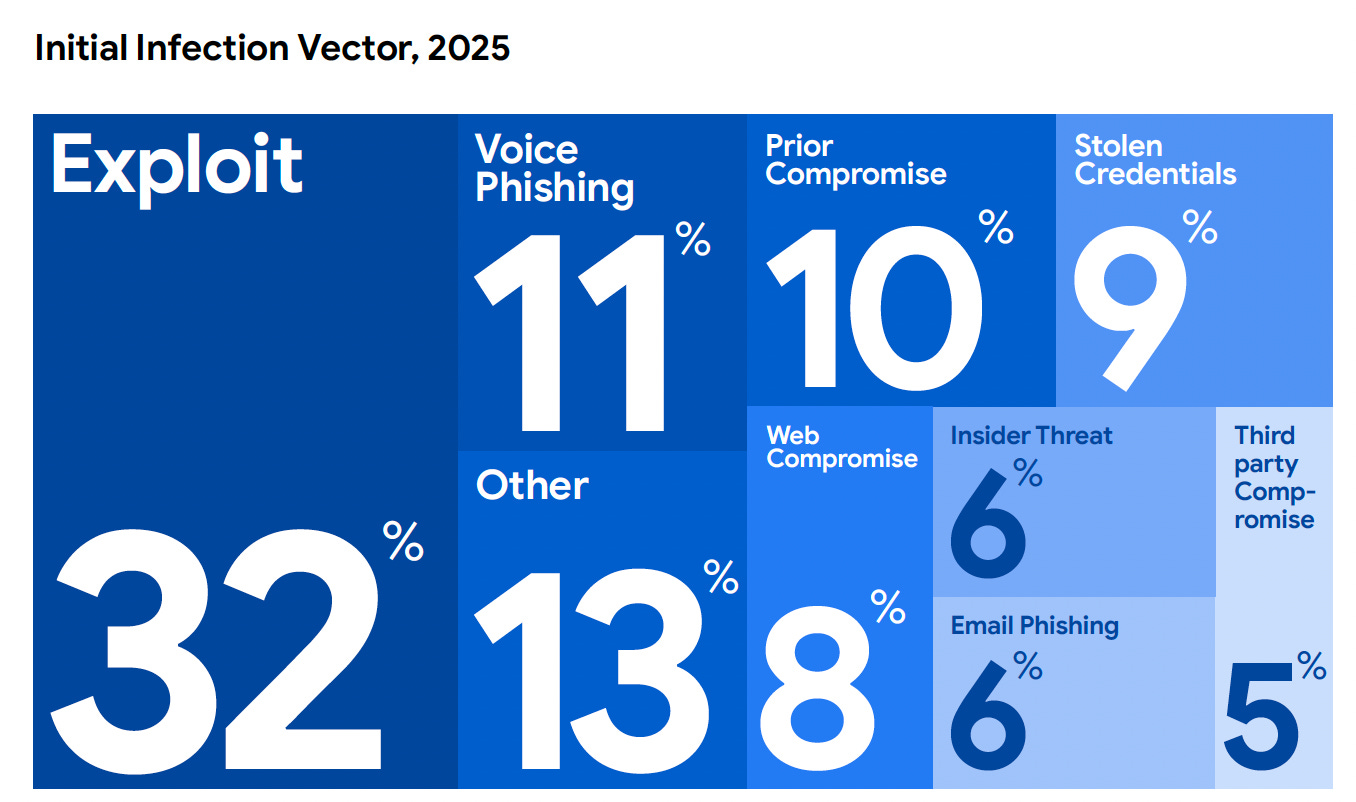
Exploitation Is the Dominant Attack Vector - Full Stop
If you take nothing else away from this year’s M-Trends report, it’s that the exploitation of vulnerabilities was the most common initial attack vector again, accounting for 32% of all intrusions Mandiant investigated. That figure is consistent with what we saw in prior years, and it cements exploitation as the leading way attackers get into organizations. As they point out, this is the 6th year running that exploitation is leading the way, and in my opinion, should put the phrase “hackers don’t hack in, they log in” to rest to some extent.
This isn’t to say that hackers don’t target credentials, they definitely do, but they more often than not are exploiting vulnerabilities as an initial attack vector as well.
This is not a blip, this is the new normal and it’s happening year-after-year. The 2024 Verizon DBIR showed exploitation tripling with a 180% increase. The 2025 DBIR followed up with another 34% year-over-year rise. Now M-Trends 2026 confirms the same pattern from a completely independent data set. When several of the most respected reports in the industry, built on different data sources and methodologies, all converge on the same conclusion, it is time to stop debating and start acting.
What makes this particularly significant from an AppSec perspective is the nature of what is being exploited. This is not just a patching problem. Mandiant reports that many of the vulnerabilities used for initial access were exploited as zero-days, meaning they were weaponized before a patch even existed. Let that sink in. Your patch management program, no matter how mature, cannot protect you against threats that don’t have patches yet. This aligns with recent writing and interviews I’ve done on the “Zero Day Clock” as well, which shows a collapse of the time-to-exploit for vulnerabilities.
I have been beating this drum for quite a while now. In “AppSec’s Runtime Revolution,” I argued that the industry’s obsession with shift-left tooling, while well-intentioned, misses the fundamental reality that vulnerabilities will always make it to production. The question is whether you have visibility and defensive capability at the application layer when they do. M-Trends 2026 provides the empirical evidence for that argument. When many of the of initial access exploits are zero-days, your security posture is only as strong as your ability to detect and respond to exploitation in real time.
The Vulnerability Backlog Is Crushing Teams
The exploitation data is alarming on its own, but it becomes even more concerning when you layer in the volume problem. CVEs continue to grow at a staggering rate. As I covered in “Context is King but Prioritization is Priceless,” CVEs were averaging roughly 135 per day in early 2025, up approximately 48% year over year. By the time I wrote “The Evolution of AppSec: From Shifting Left to Rallying on Runtime,” that number had climbed to nearly 131 per day with almost 1,000 new CVEs published every single week.
M-Trends 2026 adds critical context to these numbers. Mandiant specifically calls out that the volume of newly discovered vulnerabilities continues to outpace organizations’ ability to remediate them. Their data shows that organizations are simply unable to keep up. The result is vulnerability backlogs in the hundreds of thousands, and in large enterprise environments, the millions.
This is the vulnerability velocity problem I have been writing about. It is not just that there are more vulnerabilities. It is that the rate of discovery is accelerating while the capacity to address them is not. Organizations are adding more scanning tools, generating more findings, and creating more tickets, but they are not reducing risk at a corresponding rate. They are generating noise. And as I noted in prior articles, approximately 98% of those findings are noise that is not exploitable, not likely to be exploited, or lacking the business context needed to determine whether it matters.
The M-Trends data on exploitation timelines makes this even more pressing. When Mandiant reports that the majority of initial access exploits are zero-days, and the industry simultaneously reports that exploitation timelines have collapsed from years to hours, the traditional approach of scan, triage, and patch is fundamentally broken. You cannot prioritize your way out of a problem when the most dangerous vulnerabilities are being exploited before they even appear in your scanner.
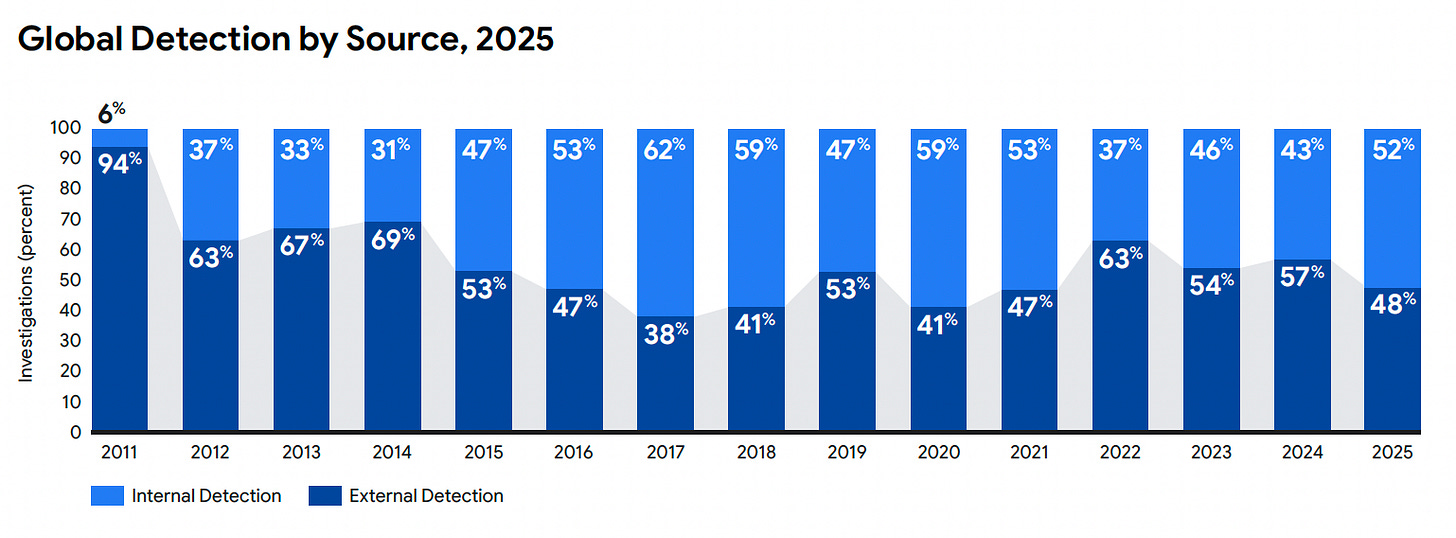
While internal detection improved to 52% in 2025, up from 43% the year prior, that still means 48% of organizations learned about their compromise from someone else. Whether that was law enforcement, CERTs, or even worse, a ransom note from an attacker, which M-Trends notes happens 14% of the time. So 14% of the time the attacker is functioning at your source of letting you know you’ve got an incident, not your team, or your expensive and complex security tech stack.
This external notification rate is a direct indictment of detection and response capabilities at the application layer. Organizations have invested heavily in endpoint detection, network monitoring, and SIEM/SOAR platforms. But application-layer attacks, exploits targeting web applications, APIs, and software supply chains, often fly under the radar because traditional security tools were not designed to see them, especially at runtime. I covered this gap extensively in “The Evolution of AppSec: From Shifting Left to Rallying on Runtime,” where I explored how traditional tools like WAFs and EDR miss critical application-layer insights. The M-Trends dwell time data reinforces exactly why Application Detection and Response (ADR) and Cloud Application Detection and Response (CADR) are emerging as critical categories.
Dwell Time: Progress, But Not the Kind You Think
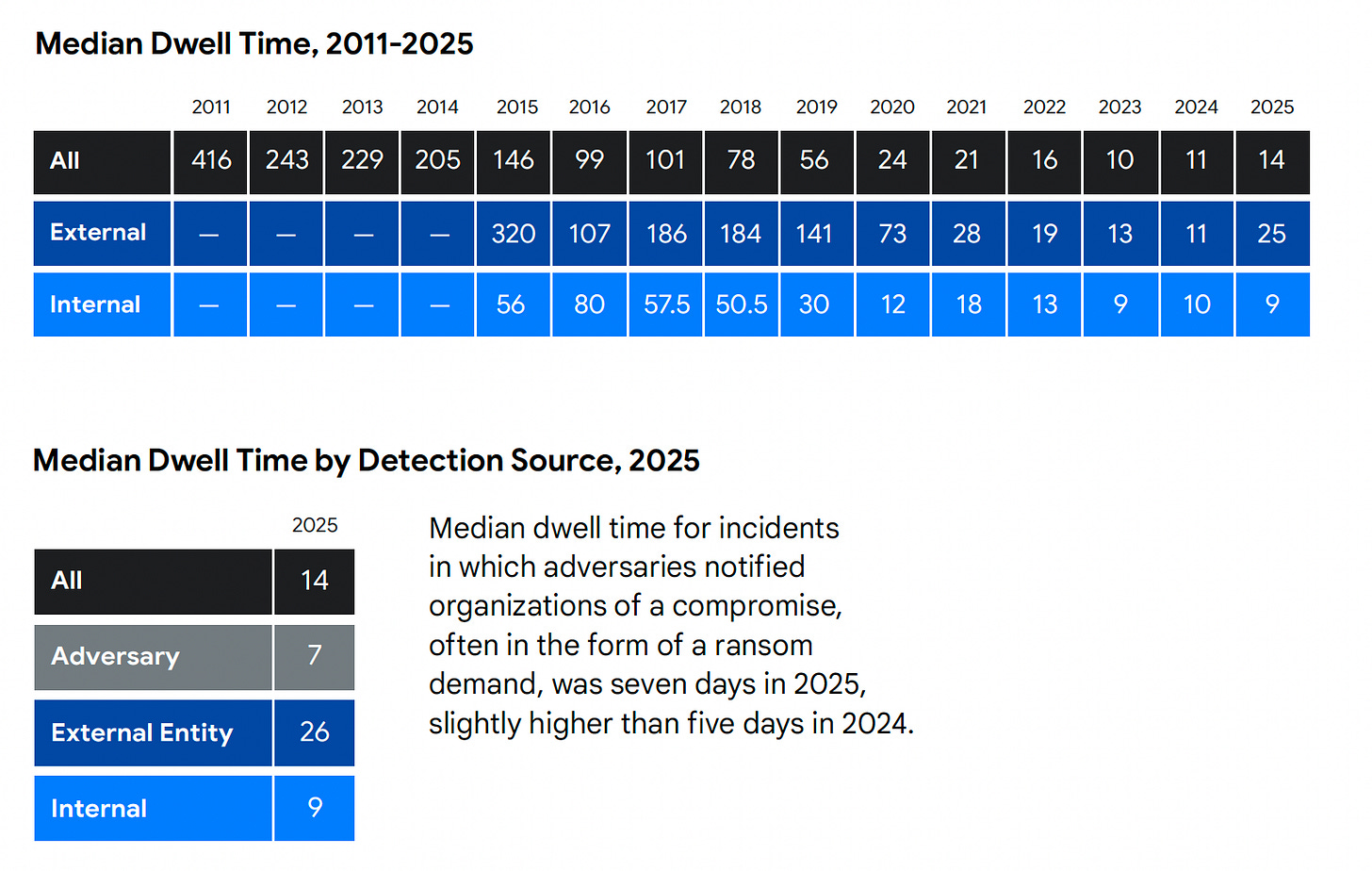
M-Trends has tracked median dwell time for over a decade, and the overall trend has been mixed. In 2024, the global median dwell time was 11 days, up from 10 days in 2023. In 2025, it climbed again, 3 more days to 14 days on average. Mandiant’s data shows that organizations are taking longer to rid their environments of malicious actors, a trend that indicates we’re losing rather than gaining ground. While we’re far better than we were a decade ago, the reversing of the improvement in minimizing dwell time is concerning.
Notably, internal detection dwell time actually improved from 10 to 9 days. The overall increase is driven by external notification cases, where dwell time jumped from 11 to 25 days, pulled up by long-dwell espionage campaigns and threat actors like North Korean IT workers.
Cloud, Edge Devices, and the Expanding Attack Surface
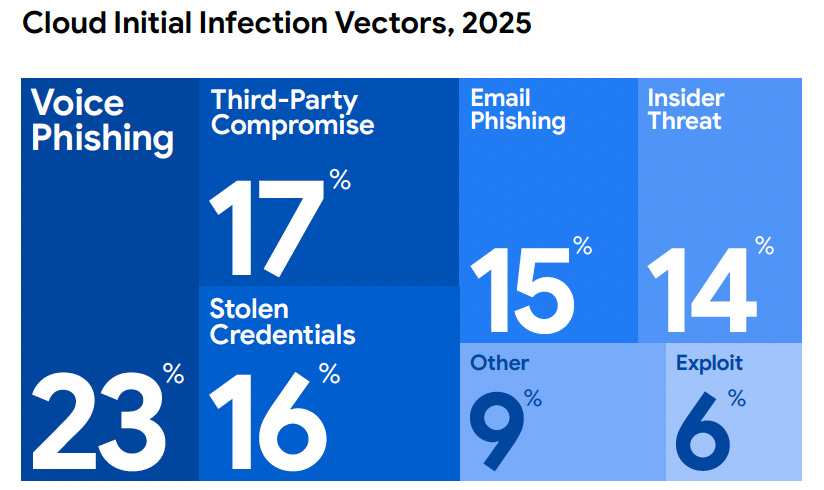
M-Trends 2026 dedicates significant attention to cloud compromises, and the findings are sobering. Mandiant reports that cloud-related incidents represented a growing share of their investigations, with identity and access management misconfigurations, overly permissive service accounts, and cross-environment lateral movement as recurring themes.
The report highlights that in many cloud intrusions, attackers moved from on-premises environments into cloud infrastructure, or vice versa, exploiting the trust relationships between hybrid environments. This is particularly relevant for application security because modern applications increasingly span multiple cloud providers, SaaS platforms, and on-premises systems. The attack surface is not a single perimeter. It is a distributed mesh of interconnected services, APIs, and data flows.
Edge devices also feature prominently in this year’s report. Mandiant calls out that network edge devices, including VPNs, firewalls, and routers, were among the most targeted systems for initial access. These devices sit at the boundary of the network, are often running outdated firmware, and are notoriously difficult to monitor with traditional security tools. When zero-day exploits target these devices, organizations frequently have no visibility into the compromise until the attacker has already established persistence and moved laterally.
The targeting of edge devices ties directly to the exploitation data. When many of the initial access exploits are zero-days, and a significant percentage of those target edge infrastructure, organizations need to rethink their defensive architecture. Relying on the device vendor to ship a patch in time is not a strategy, it is a hope.
AI, Vibe Coding, and the Coming Software Supply Chain Reckoning
M-Trends 2026 addresses AI’s role in the threat landscape, noting that threat actors are increasingly experimenting with AI for reconnaissance, social engineering, and operational planning. While Mandiant stops short of declaring AI-generated exploits a widespread problem today, the trajectory is clear, AI is lowering the barrier to entry for attackers while simultaneously expanding the attack surface through AI-generated code and AI-powered applications.
This is where the AppSec implications get particularly acute. I covered this extensively in “Vibe Coding Conundrums,” where I examined the rise of AI-assisted and AI-generated development. When Y Combinator reports that 25% of startups in their current cohort have codebases that are almost entirely AI-generated, and research shows that over 60% of AI-generated solutions contain security vulnerabilities, we are looking at a massive expansion of the vulnerable code base that is about to hit production environments.
The M-Trends data on exploitation timelines and zero-day prevalence makes this particularly dangerous. If AI-generated code introduces vulnerabilities at scale, and exploitation timelines continue to compress, the window between a vulnerability existing and an attacker exploiting it shrinks to near zero. Traditional AppSec programs that rely on code scanning and developer remediation cannot keep pace with this dynamic. The code is being generated faster than it can be reviewed, and the exploits are being developed faster than patches can be shipped, or even developed.
This is compounded by the rise of agentic AI systems in enterprise environments. Agents that autonomously interact with APIs, databases, and external services create entirely new attack surfaces that traditional security tools were not designed to monitor.
When an AI agent can browse the web, execute code, and chain tool calls together, the potential for exploitation is not limited to a single vulnerability. It extends to the entire set of actions and integrations the agent has access to.
M-Trends does not address agentic AI specifically, but the exploitation patterns it documents are directly applicable to agent-based architectures. The same zero-day exploitation, credential theft, and lateral movement techniques that Mandiant observes in traditional environments will be used against agentic systems, with the added challenge that agents can be manipulated through prompt injection and tool abuse in ways that have no parallel in traditional software.
Couple this with the rise of autonomous and AI-driven malicious activity and it’s a scary combination of trends for sure.
The Bottom Line
M-Trends 2026 is not a comfortable read for anyone in cybersecurity. The data is clear, exploitation is dominant, zero-days are the norm, detection is lagging, and the attack surface is growing in every direction. AI is accelerating all of these trends simultaneously, both on the attacker side and through the explosion of AI-generated code that is expanding the vulnerable surface area.
But the report also points toward the answer. Runtime visibility, contextual prioritization, application-layer detection and response, and a willingness to embrace AI and Agents FOR security, making security an early adopter much like our business peers and attackers alike. The legacy static, cumbersome approaches of security are simply buckling under the pace of the current AI-driven paradigm, and that is showing cracks across AppSec, SecOps, GRC, OffSec and everything in between.
The organizations that take these lessons seriously and invest in the capabilities to act on them will be the ones that bend the curve. The rest will continue to show up in next year’s report.
The data is in, the trends are undeniable, the question is whether organizations are ready to evolve fast enough to meet them.


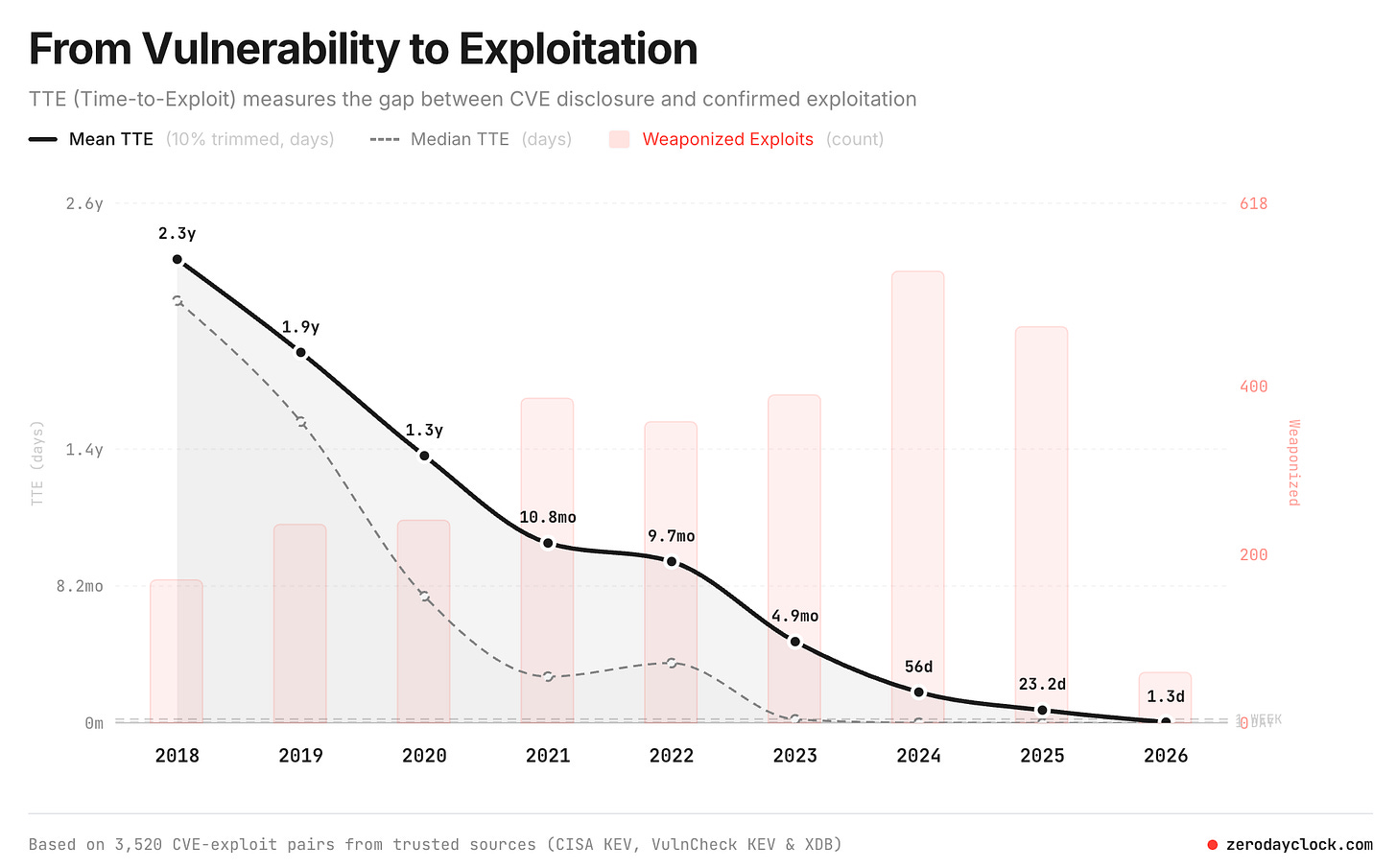
The exploitation velocity point lands hard. The window is not just shrinking - for some CVEs it is now measured in hours, not days. That breaks the prioritization models most security teams still run.
From a PM angle: most teams are tracking the wrong metric. Time-to-patch as the SLA sounds right until exploitation happens at hour 6 and your patch cycle is day 3. The actual signal is mean time between disclosure and active exploitation, and almost nobody has that instrumented.
The AI and agentic threads in this M-Trends are worth a separate read. Attack surface changes fundamentally when the agent can act on its own.