Security in the Middle
The Data Behind Cybersecurity's Most Overlooked Threat Surface
I’m excited to share my deep dive of The Security Middle Child report, a collaboration between myself and the team at Intruder. This report surveyed 502 senior security decision-makers at midmarket organizations (400 to 6,000 employees) across the U.S. and UK to understand how these teams are managing their security posture, where they feel confident, and where the cracks are forming.
If you’ve followed my writing on vulnerability management, exposure management, and the cybersecurity poverty line, this report brings hard data to the themes I’ve been exploring for years. Let me walk through the key findings and what they mean for the industry.
Why the Midmarket Is the Industry’s Blind Spot
The cybersecurity industry has a well-documented habit of building for the largest enterprises and hoping the solutions trickle down. Research reports, vendor roadmaps, and conference keynotes are overwhelmingly oriented toward Fortune 500 security programs. On the other end of the spectrum, small businesses are acknowledged as underserved but largely left to fend for themselves. The midmarket, organizations large enough to be targeted but too resource-constrained to operate like an enterprise, gets overlooked.
This is the dynamic that Wendy Nather identified over a decade ago when she coined the concept of the cybersecurity poverty line in her 2013 RSA presentation. I’ve had the privilege of exploring this concept with Wendy and Casey Ellis on the Resilient Cyber podcast, where we discussed how systemic challenges disproportionately impact organizations that lack the budgets and staffing of enterprise programs. Ross Haleliuk made a compelling case in a piece him and I collaborated on titled lifting the world out of cybersecurity poverty that vendors continue to chase the same few thousand well-resourced buyers while ignoring millions of organizations that need help just as urgently.
This report puts numbers behind that argument. The midmarket is not a niche, it is where the majority of economic activity happens, and it is where the gap between threat reality and security capability is most pronounced.
Surface-Level Confidence, Deeper Fragility
One of the most striking findings in the report is the gap between stated confidence and operational reality. On the surface, the numbers look encouraging: 94% of respondents said they are confident in their ability to identify critical risks quickly. That is a strong headline number, and it would be easy to read it and move on.
But dig deeper and the picture shifts considerably. That confidence is not evenly distributed. Among C-level executives, 65% expressed high confidence, while only 36% of middle managers said the same. This is a meaningful gap because the people closest to the actual work of managing vulnerabilities, triaging alerts, and responding to incidents are far less confident than the executives who report on the program’s health to boards and stakeholders.
This confidence gap has real implications. If leadership believes the security program is more capable than it actually is, resourcing decisions, risk acceptance, and strategic priorities are all being informed by an inaccurate picture. As I’ve written before in the context of exposure management metrics (another excellent Intruder report), the metrics we report upward need to reflect operational reality, not just what boards want to hear, even if the truth is uncomfortable. Failing to be honest can have ramifications for getting funding and support for operational security needs.
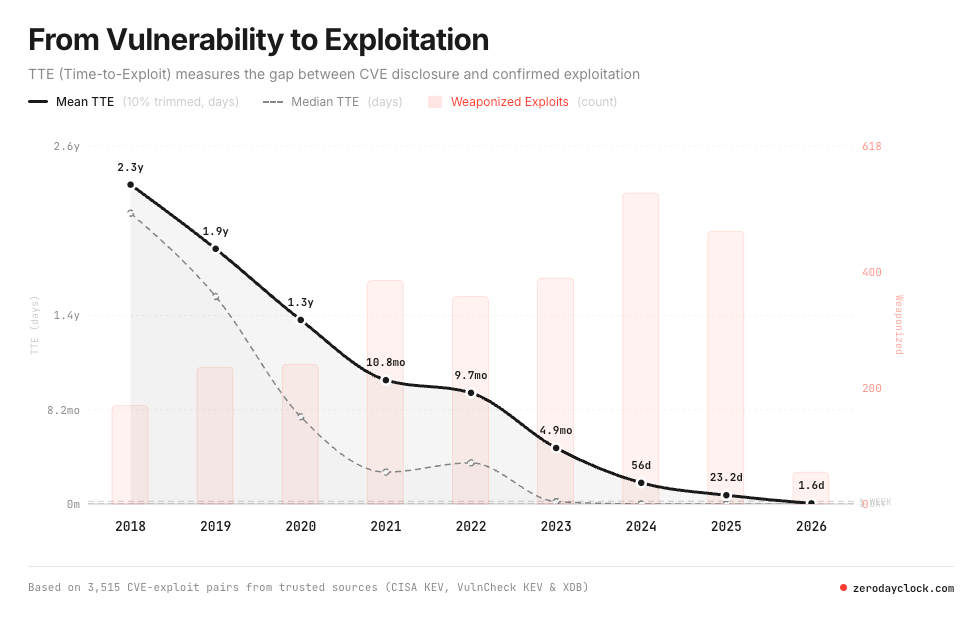
The fragility shows up in other data points as well. When asked how long it would take to assess their exposure to a newly disclosed critical zero-day vulnerability, 51% of respondents said it would take at least a week. In a world where threat actors are weaponizing vulnerabilities in days, a week-long assessment window represents significant risk. This is not a confidence problem. It is a capability problem, and it affects organizations that genuinely believe they are in good shape.
If a week doesn’t sound concerning, you should check out the Zero Day Clock, and my recent article “The Zero Day Clock is Ticking”, where I demonstrate how in 2026, the majority of exploited vulnerabilities are weaponized before they are even publicly disclosed.
Stretched Teams and Expanding Attack Surfaces
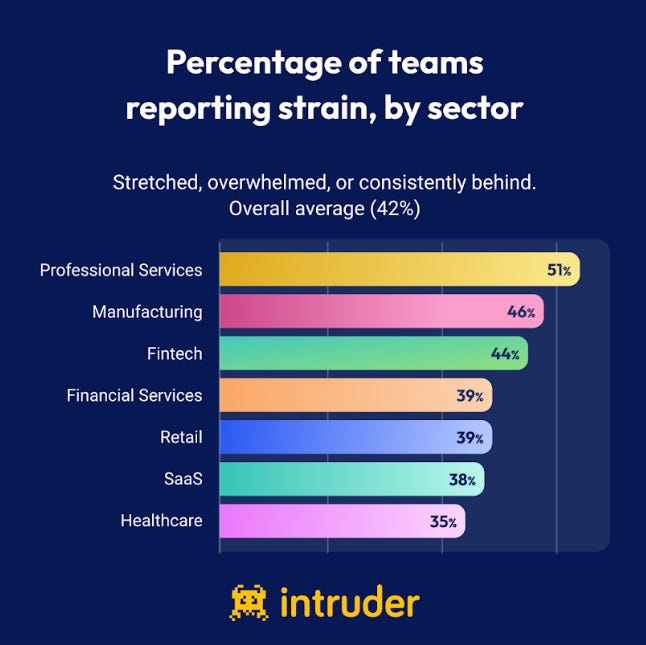
The report paints a clear picture of teams under pressure. On average 42% of security teams described themselves as stretched, overwhelmed, or consistently behind, and in some sectors it’s even worse. These are not teams that have given up. They are teams doing their best with limited headcount, growing responsibilities, and an attack surface that will not stop expanding.
And expand it has, with 91% of respondents reported growth in their digital estate over the past 24 months, with 38% describing that growth as significant. Cloud adoption, remote work infrastructure, SaaS sprawl, digital transformation initiatives and now the AI wave have all contributed to a broader and more complex attack surface. The challenge is that security staffing and tooling have not scaled proportionally, and honestly, this isn’t a problem we can “hire” ourselves out of either.
This dynamic is familiar to anyone who has worked in or around midmarket security. You have a small team, sometimes just a handful of people, responsible for everything from endpoint protection to cloud security to compliance. Every new system, every new SaaS application, every new cloud workload adds to the surface area they need to monitor and protect. As I wrote in Effective Vulnerability Management, the math simply does not work when the attack surface grows faster than the team’s capacity to manage it. Something has to give, and it is usually depth of coverage coupled with implicit risk acceptance due to bandwidth constraints.
Tooling That Does Not Fit
One of the most actionable findings in the report is around tooling. 44% of respondents said they have either outgrown their current security stack or are relying on stitched-together point solutions that do not integrate well. This is a direct consequence of the industry’s failure to build for the midmarket.
Enterprise security platforms are often too expensive, too complex, and assume more staff than midmarket teams can field. 46% of respondents specifically noted that enterprise-grade platforms assume more budget and staffing than their organizations can support. On the other hand, lightweight tools designed for small businesses often lack the depth and sophistication that midmarket organizations need.
The result is what many practitioners will recognize, a patchwork of tools that don’t talk to each other, creating visibility gaps and making it difficult to get a unified view of the organization’s exposure. In fact, some security vendors have even tried to build aggregators, to solve for this lack of cohesion among the security tech stack. This is exactly the environment where misconfigurations go unnoticed, critical findings slip through the cracks, and teams spend more time managing tools than managing risk.
This is shining through in the report’s data too, with 26% citing navigating too many security tools as a top operational challenge, alongside issues such as too many noisy alerts and the inability to measure and report on cyber hygiene and risks. Ironically, 33% of those surveyed also said they plan to add more security solutions this year. This points to the reality that legacy tooling isn’t keeping pace with technological innovation and the risk landscape, but trying to purchase our way out of it with products is only creating unintended consequences as well.
The midmarket’s perception of security tool vendors is clear too, with nearly half stating they feel like enterprise security tools assume they have more budget or staff than they do, or needing to stitch together tooling to cover gaps.
AI, Automation, and the Promise of Doing More with Less
Given the resource constraints, it is not surprising that midmarket organizations are looking to AI and automation as a way to close the gap. 49% of respondents identified AI and automation as their top investment priority, and 41% reported already adopting AI-powered penetration testing capabilities.
This is an encouraging signal, but it comes with important caveats. Automation can absolutely help with the volume problem, scanning more frequently, triaging more efficiently, and reducing the manual burden on stretched teams. But automation without context can also create noise. If AI-powered tools are generating more findings without helping teams understand which ones actually matter in their specific environment, the net effect can be more work rather than less.
The organizations that will get the most value from AI investments are the ones that pair automation with risk-based prioritization, focusing AI-generated insights on the intersection of vulnerability severity, asset criticality, and real-world exploitability. As I have discussed in prior writing, the transition from traditional vulnerability management to Continuous Threat and Exposure Management (CTEM) depends on this kind of contextual analysis, not just faster scanning.
Board Engagement Remains a Gap
Perhaps the most sobering finding in the report is the state of board-level engagement with cybersecurity risk. Only 9% of respondents said that cyber risk is discussed at the board level. For all the industry conversation about cybersecurity as a board-level issue, the data suggests that for midmarket organizations, this aspiration is far from reality.
Without board engagement, security teams struggle to secure the resources and strategic support they need. Security remains a cost center rather than a strategic function, and investment decisions are reactive rather than proactive. This is a cycle that is difficult to break, especially for teams that lack the bandwidth to build the executive-facing reporting and risk narratives that drive board conversations.
What the Industry Needs to Do Differently
The findings in this report should be a call to action for the cybersecurity industry, and I mean the entire ecosystem, vendors, investors, policymakers, and practitioners.
Vendors need to stop treating the midmarket as a scaled-down version of the enterprise. Midmarket organizations have fundamentally different constraints and needs. They need solutions that are affordable, self-service, and designed for small teams. That means simplified deployment, integrated platforms that reduce tool sprawl, and pricing models that do not punish organizations for growing.
The industry needs to bridge the confidence gap. Security leaders at midmarket organizations need better frameworks for assessing and communicating their actual security posture, not just dashboards that tell a comfortable story. As Wendy Nather has cautioned, metrics can create a false sense of security if they are not grounded in operational reality.
AI and automation investments need to be paired with context. The promise of AI in security is real, but it will only deliver for midmarket organizations if it helps them prioritize, not just detect. Tools that generate more findings without helping teams determine what matters will only deepen the overwhelm.
Board engagement must improve. The 9% figure on board-level cyber risk discussion should be alarming. Industry groups, regulators, and security leaders all have a role in making cybersecurity a strategic conversation at midmarket organizations, not just an IT line item.
The issue of course in the above items is that many of the security product vendors are facing their own competing incentives. For example, many security product vendors are venture capital backed, facing fierce competition in their categories, pushed to land big logos to show early momentum, and wanting to capture larger deal sizes to signal traction to their investors.
Final Thoughts
This is another excellent report from the Intruder team, highlighting systemic challenges affecting large parts of the broader cybersecurity ecosystem. It fills a critical gap in our understanding of how the midmarket, the true middle child of cybersecurity, is navigating a threat landscape that shows no signs of slowing down.
The data tells a story that should resonate with anyone who has worked in or alongside these organizations. They are doing more than the industry gives them credit for, but they are doing it under conditions that are not sustainable without better tools, better frameworks, and more attention from the ecosystem that is supposed to serve them.
You can find the full Security Middle Child report here.