The Compliance Revolution is Here: From Commoditized Rubber Stamps to Agentic AI
How platform services, AI agents, and a credibility crisis are reshaping GRC from the ground up
We’ve built an entire industry around proving we’re secure on paper while getting breached in production.
Throughout my 20+ year cybersecurity career, I’ve spent more time than I’d like to admit swimming in the alphabet soup of compliance frameworks. I’ve written about it extensively, including in my piece GRC is Ripe for a Revolution, where I laid out how the how we do compliance is fundamentally broken , where static documents, snapshot-in-time assessments, system sampling, and legacy GRC platforms that function as analog relics in a digital world.
Since publishing that piece, the landscape has only accelerated.
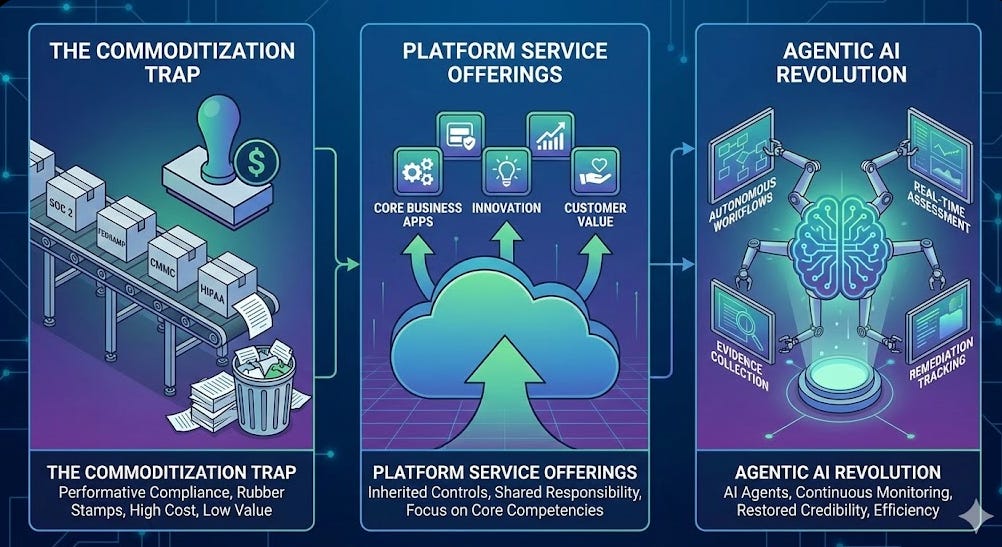
We’re watching three simultaneous forces converge that I believe will fundamentally reshape GRC: the commoditization of compliance creating a credibility crisis, the rise of platform service offerings absorbing undifferentiated heavy lifting, and the emergence of agentic AI that promises to restore both efficiency and integrity to a field in desperate need of both.
Let’s dig in.
Interested in sponsoring an issue of Resilient Cyber?
This includes reaching over 31,000 subscribers, ranging from Developers, Engineers, Architects, CISO’s/Security Leaders and Business Executives
Reach out below!
The Commoditization Problem
Compliance has become commoditized, and not in the good way.
The most visible symptom has been the SOC 2 industrial complex. Over the past several years, we’ve watched an entire cottage industry emerge around getting organizations their SOC 2 report as fast and cheaply as possible. Platforms emerged promising SOC 2 readiness in weeks, bundled with auditor partnerships that, let’s be frank, sometimes looked more like revenue-sharing arrangements than independent assessments.
The community hasn’t been quiet about this. If you’ve spent any time on LinkedIn or in GRC practitioner circles, you’ve seen the heated discourse around what many call “rubber stamp” SOC 2 reports. Practitioners openly describe receiving SOC 2 reports from certain audit firms and essentially throwing them in the trash because they hold no meaningful assurance value. The conversation has gotten loud enough that terms like “SOC-in-a-box” have become part of the vernacular, and for good reason.
For $9,000, you can get a GRC automation platform and a SOC 2 Type 2 report issued by an AICPA-accredited audit firm.
If the industry standard for security assurance has an entry tax of $9,000 and a rubber stamp, what exactly are we assuring? Because it certainly isn’t security.
But SOC 2 is just the most talked-about example. The commoditization problem and the cottage industries it has spawned, extends across the compliance landscape, across various frameworks.
Look at FedRAMP.
Achieving FedRAMP authorization can take up to three years and costs millions. That cost doesn’t just go to security engineering work, a massive chunk of it flows to the sprawling ecosystem of Third Party Assessment Organizations (3PAOs), FedRAMP consultants, advisory firms, and compliance shops that have built entire businesses around helping companies navigate the labyrinth.
Tech companies find themselves writing six- and seven-figure checks to consultants just to understand the process, prepare the documentation, and shepherd their authorization package through the bureaucracy. The compliance work becomes a tax on innovation, and the consultants become toll collectors on the road to selling to the government.
The DoD’s Cybersecurity Maturity Model Certification (CMMC) tells a similar story.
After the DoD’s self-attestation model for 800-171 failed spectacularly, with Defense Industrial Base vendors claiming compliance while nation-states like China pilfered sensitive weapons data and intellectual property, we got the Cybersecurity Maturity Model Certification.
Well-intentioned?
Absolutely.
But it has spawned its own cottage industry of Registered Practitioners (RPs), Registered Provider Organizations (RPOs), CMMC assessors, and an army of consultants selling “CMMC readiness” packages to the hundreds of thousands of DIB companies scrambling to figure out what they actually need to do. Many of these small and mid-size manufacturers are spending disproportionate sums on advisory services just to understand the requirements, let alone actually meet them.
The most unfortunate aspect of the FedRAMP and CMMC is they essentially impede the public sector, those who rely on digital citizen services and warfighters access to innovative commercial technologies, all at a time when public trust in institutions is already struggling.
The pattern repeats across HIPAA, PCI DSS, GDPR, EU AI ACT, CRA and the ever-growing alphabet soup of frameworks. Each one creates its own ecosystem of consultants, assessors, and intermediaries. Organizations, especially smaller ones without deep compliance expertise, are forced to pay a compliance tax to an industry of middlemen before they can even begin the actual security work or at least fully understand what must be done.
The consultants aren’t the problem per se, as many of them do genuinely care and want to help businesses become secure and compliant; the complexity that necessitates their existence is, and often serves as a tax to expand your total addressable market (TAM).
This dynamic has had a corrosive effect on the entire field.
It feeds directly into the most weaponized phrase in cybersecurity: “compliance doesn’t equal security” a phrase I am not a fan of, and tried to address in my article “Compliance Does Equal Security - Just Not the Elimination of Risk”.
But, here’s the uncomfortable truth, when compliance is conducted as a paper-based, snapshot-in-time, check-the-box exercise with auditors who lack technical depth, platforms optimizing for speed over substance, and organizations spending more on navigating the compliance maze than on actual security improvements, that phrase is right.
We’ve made it right through our own practices.
We did this to ourselves.
Platform Services: Absorbing the Undifferentiated Heavy Lifting
While the SOC 2 drama has been playing out on the commercial side, something more structurally interesting has been happening in the federal and regulated space: the rise of platform service offerings that absorb the undifferentiated heavy lifting of compliance from individual organizations. Several of these are following models pioneered by the DoD’s Software Factory ecosystem, which involved shared services, platform engineering, security control inheritance and the alleviation of compliance toil related to achieving DoD Authority to Operate (ATO) status.
Consider what’s happening with FedRAMP.
Achieving FedRAMP authorization can take several years and cost millions of dollars. That’s a prohibitive barrier for the vast majority of software companies, especially the innovative startups that the government arguably needs most. It often serves as a moat for entrenched incumbents with deep pockets who rarely deliver disruption or innovation but have the financial resources that newer entrants and SMBs lack.
The result?
The FedRAMP Marketplace lists roughly 500 authorized applications while commercial marketplaces like AWS and Salesforce host thousands each. It is also worth noting that a large portion of the FedRAMP Marketplace of authorized cloud service offerings (CSO) has come recently, with efforts such as FedRAMP 20x and under the leadership of Pete Waterman, both of which are critical and doing amazing work, especially given what they inherited. That said, FedRAMP 20x still has a lot of work to be done, and warrants its own discussion. In fact, it is one I broke down in my interview with guest Kenny Scott in an episode of Resilient Cyber titled “Following the Future of FedRAMP”.
Companies like Knox, Second Front Systems, and Palantir (through its FedStart offering) have recognized this gap and are building platform services that fundamentally change the equation.
Knox provides a managed federal cloud where software vendors can leverage their authorized platform and inherit the a large share of security controls, reducing the FedRAMP timeline from years to roughly 90 days. Second Front’s Game Warden platform does something similar for DoD Authorization to Operate (ATO)/FedRAMP, enabling software vendors to leverage inheritable security controls across DoD Impact Levels 2 through 6, JWICS, and up to FedRAMP High.w
The model is elegant in its simplicity: rather than every individual software company independently toiling through hundreds of NIST 800-53 controls, the platform provider has already met them. Vendors inherit those controls and focus only on their application-layer security. This is the Shared Responsibility Model applied to compliance itself.
What I find most compelling about this trend is that it directly addresses the security control inheritance and reciprocity problem I’ve written about previously. In modern software development, the overwhelming majority of applications are built atop hyper-scale CSPs or managed platforms that have already met rigorous compliance requirements.
The idea that every individual vendor needs to independently assert compliance with controls the platform already satisfies is not just inefficient, it’s wasteful and counterproductive.
These platform service offerings represent compliance IaaS/PaaS, much like CSPs have done. They commoditize the undifferentiated work so organizations can focus on what actually matters: securing their specific application and data and most importantly, delivering value to their customers and focus on their core competencies, which isn’t focused on meeting security controls and compliance frameworks.
While not platform-specific, I also want to highlight others offering managed service offerings that alleviate the compliance toil. Another notable player I’ve covered previously is Chainguard, who through their hardened base images and zero CVE offerings, alleviate the cumbersome nature of vulnerability management and SLA’s, which are often tied to compliance requirements for customers. I broke this down in great detail in my article “CVE Cost Conundrums: Unpacking Chainguard’s 2025 Cost of CVEs Report”.
Their report demonstrated how companies are often spending hundreds of thousands of dollars to remediate vulnerabilities and harden container images, often to meet regulatory requirements. This of course is an activity that isn’t their core competency and isn’t tied to why those companies ever started their businesses.
Chainguard has reached unicorn status with a > $1B valuation, and now there are various other startups looking to play in the space as well.
Agentic AI: The Real Revolution
Now, here’s where things get genuinely interesting.
We’ve seen a wave of GRC automation platforms over the past several years, Drata, Vanta, and others, that have done meaningful work modernizing GRC from the legacy RSA Archer and eMASS era. They brought automated evidence collection, continuous monitoring, integration with modern cloud tooling, and streamlined audit workflows. That was a necessary and important first step.
But the next wave is different.
It’s not just automation, it’s autonomy and it’s underpinned by Agentic AI.
A growing cohort of innovators are now applying agentic AI to GRC use cases, and the implications are significant. Take Complyance, for example. They’ve built an AI-powered enterprise GRC platform with purpose-built AI agents across the compliance lifecycle, evidence review agents that flag gaps before audits, vendor questionnaire review agents that surface risky responses, policy drafting agents, risk treatment planning agents, and customer trust agents that can draft responses to security questionnaires in minutes rather than days.
They recently raised a $20M Series A led by Google Ventures, signaling serious market validation for this approach. They claim a 70% reduction in manual GRC work, which if even directionally accurate, is transformational for resource-constrained GRC teams. It also speaks directly to the ambitions of agentic AI, which is freeing humans from the laborious tedium that consumes much of knowledge work, including in GRC, to focus on more value added activities for their respective organizations.
They’re not alone.
Anecdotes has introduced what they call “Agentic GRC” with an agent studio where enterprises can build custom AI agents that execute complete compliance workflows autonomously, from trigger through analysis to action.
Their approach is built on a data engine that normalizes information from 230+ enterprise integrations, giving agents the contextual awareness to make meaningful decisions rather than generic suggestions.
Existing incumbents such as Drata has unveiled its own agentic AI vision, including MCP (Model Context Protocol) integration that enables their compliance data to flow natively into AI environments like Claude and developer IDEs. Their vendor risk management agent can autonomously evaluate third-party vendors, score risk, and produce audit-ready outputs. Sprinto, Scytale, Comp AI, and others are all racing to embed agentic capabilities across the GRC lifecycle.
What makes the agentic approach genuinely different from earlier automation waves is the shift from reactive alerting to autonomous workflow execution. Traditional continuous control monitoring detects a gap and sends an alert. Then a human reads it, figures out what to do, routes it to the right team, and manually tracks resolution.
Agentic GRC completes the entire cycle: the agent detects the gap, analyzes impact across mapped frameworks, creates a remediation ticket with full context, notifies the control owner with recommended steps, and monitors until resolution is verified.
This is not incremental improvement, it is a category shift.
Restoring Credibility to GRC
Here’s why all of this matters beyond efficiency gains.
The cybersecurity industry has a well-known workforce shortage. ISC2 and others regularly publish eye-popping statistics about millions of unfilled positions (which I strongly believe can be debated, but that’s another story).
GRC teams in particular are chronically understaffed, overworked, and buried in manual processes that consume their time and prevent them from doing the strategic work that actually improves security posture. The manual toil also prevents them from building technical expertise and contributes to their reputation of being “non-technical” as they spend much of their time in tools such as Excel and PDF, rather than in Cloud, Kubernetes, Microservices, and most recently, AI.
AI agents don’t just address this workforce challenge, they fundamentally restructure how GRC work gets done. When agents handle evidence collection, questionnaire responses, control monitoring, and remediation tracking, human GRC professionals are freed to do what humans do best: exercise judgment, build relationships with business stakeholders, interpret ambiguous risks, and drive strategic security improvements. These are the sort of activities that truly make a strategic impact for business outcomes.
But the opportunity here goes beyond operational efficiency. It goes to the very credibility of the GRC field itself.
The “compliance doesn’t equal security” critique exists because compliance as historically practiced has been largely performative, with static documents written once and shelved, annual assessments that capture a single moment in time, system sampling that covers a fraction of the environment, and rubber-stamped reports that provide a false sense of assurance.
We pretend to implement controls, they pretend to test them, and the board pretends to understand the report.
AI-driven continuous assessment fundamentally changes this equation. When compliance posture is assessed in real-time across the full environment, when evidence is collected and validated continuously rather than gathered in a frenzy before audit season, when control gaps are detected and remediated autonomously, compliance starts to actually mean something again. It becomes a genuine signal of security posture rather than a performative exercise.
Agentic AI, combined with platform services that handle undifferentiated compliance heavy lifting, and modern GRC platforms that replace legacy document repositories with API-driven continuous assessment, this is how we bring GRC out of the dark ages and into the digital domain.
The revolution isn’t coming. It’s here. The question is whether the industry will embrace it or continue clinging to the paper-based practices that have undermined its credibility for decades.
If we want to stop hearing “compliance doesn’t equal security,” then we need to stop participating in the performative arts that make that phrase true.