Your Cloud Workspace Is a Treasure Chest -Most Organizations Should Treat It It Like One
There is a reason attackers love email. It is the front door to every organization, the repository for the most sensitive communications a business produces, and the single richest target for credential theft, business email compromise, phishing, and data exfiltration.
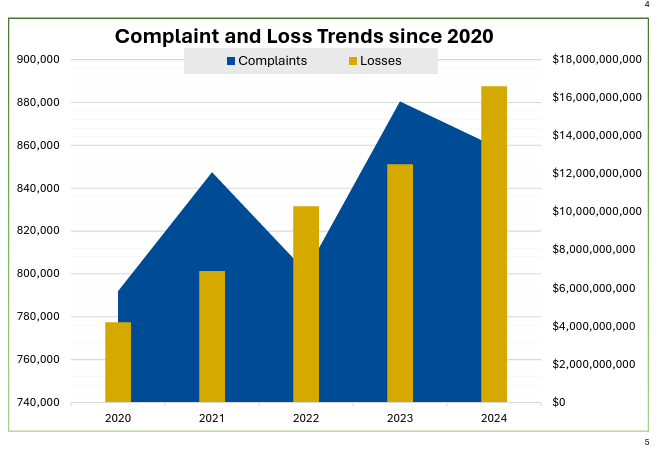
The FBI’s 2024 IC3 report tallied $16.6 billion in cybercrime losses, up 33% year over year, with business email compromise among the costliest categories.
IBM’s 2025 Cost of a Data Breach report continues to put the average breach in the multimillion-dollar range, and yet, despite all of this, the way most organizations approach email security has barely evolved in over a decade.
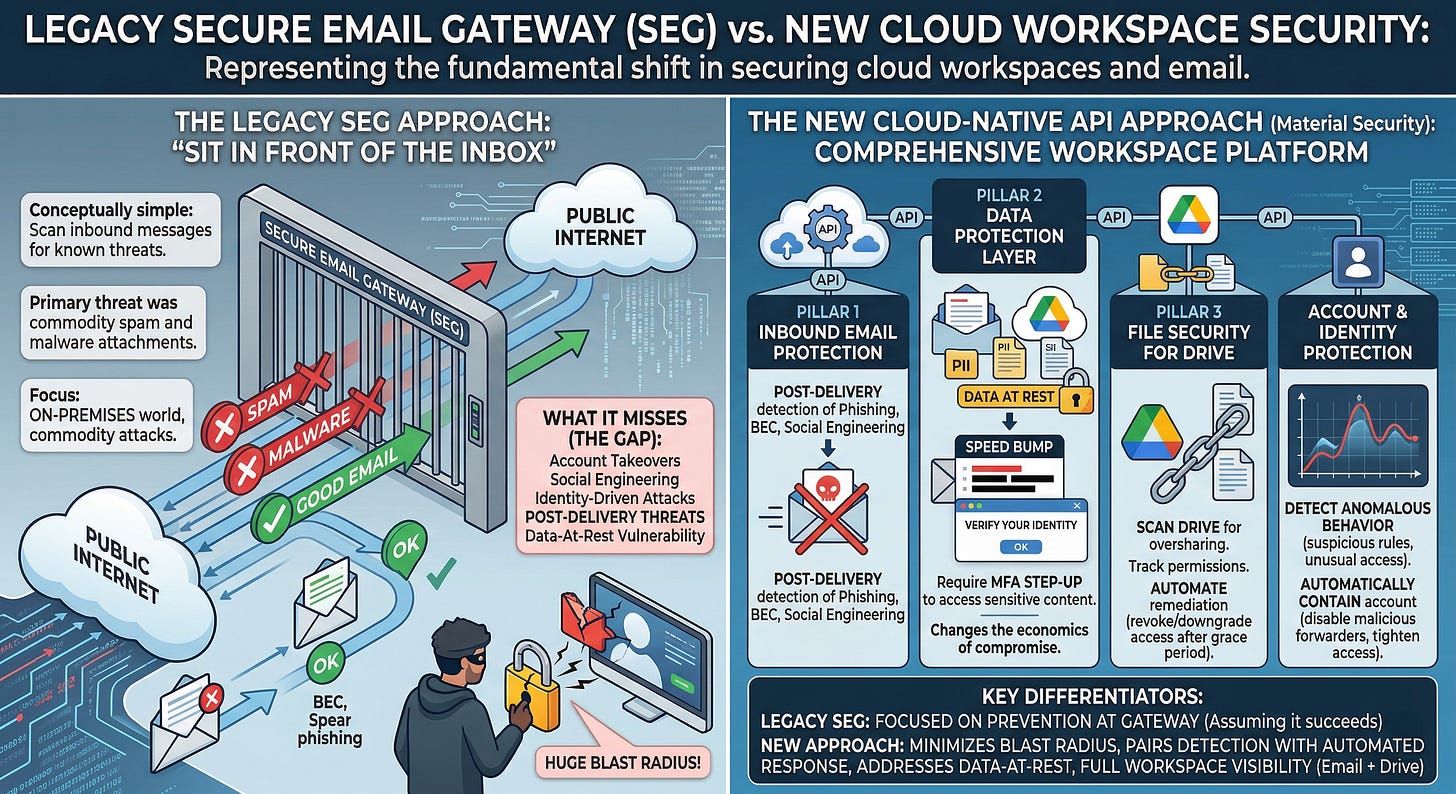
The dominant paradigm is still the Secure Email Gateway, or SEG. The SEG model is conceptually simple. Sit in front of the inbox, scan inbound messages for known threats, block what looks malicious, and let everything else through. It was built for a world where email lived on-premises and the primary threat was commodity spam and malware attachments.
That world no longer exists. Email now lives in cloud platforms like Google Workspace and Microsoft 365. The most costly attacks rely on social engineering, account takeover, and living-off-the-land techniques that look clean at the gateway and only turn malicious after a user engages. SEGs were not designed to catch those attacks, and they are showing their age.
The cloud-native API-based email security vendors emerged to address some of these gaps, offering post-delivery detection that catches threats the gateway misses. That is a meaningful improvement, but it still operates within the same fundamental paradigm.
Scan for threats, detect bad things, and respond after the fact. What it does not address is the much larger problem hiding in plain sight. The data already sitting in your inbox and drive that represents the real blast radius when an account is compromised.
This is where Material Security takes a fundamentally different approach, and after getting a firsthand demo of their platform and spending time with their team, I wanted to break down what makes their model both comprehensive and distinct.
The Data-at-Rest Problem Nobody Talks About
Here is the question that most email security products do not ask. What happens after the attacker gets in?
The average enterprise inbox contains years of accumulated email. Sensitive data that was shared in context at the time but now sits in perpetuity, fully accessible to anyone who gains access to the account. Think about what lives in your inbox right now. Contracts, financial data, customer records, credentials, board communications, legal discussions, M&A details, PII, PHI, PCI data. All of it searchable, all of it accessible, all of it sitting at rest with no additional protection beyond the account credential that was already compromised. This fundamentally fails the longstanding principle of defense-in-depth.
Material Security was founded on the insight that this data-at-rest problem is the real email security challenge. Their original product innovation was not another inbound threat detection engine. It was a mechanism to protect the sensitive data already sitting in the inbox by adding an MFA step-up requirement before that data could be accessed.
The concept is straightforward but powerful. Classify emails containing sensitive data, redact that content, and require the user to authenticate through an out-of-band MFA challenge before the original content is revealed. Valid users pass the check with minimal friction. Attackers who have compromised the account hit a wall, rather than having broad access to everything within it.
Material’s approach fundamentally changes the economics of account compromise. In a traditional environment, a compromised account gives the attacker full access to everything in the inbox and Drive from day one.
With Material in place, the attacker can see that sensitive emails exist but cannot access the content without passing an authentication challenge they do not control. Every access attempt is logged and can trigger an alert, turning the inbox from a silent treasure chest into an active tripwire.
Beyond Phishing - A Comprehensive Workspace Platform
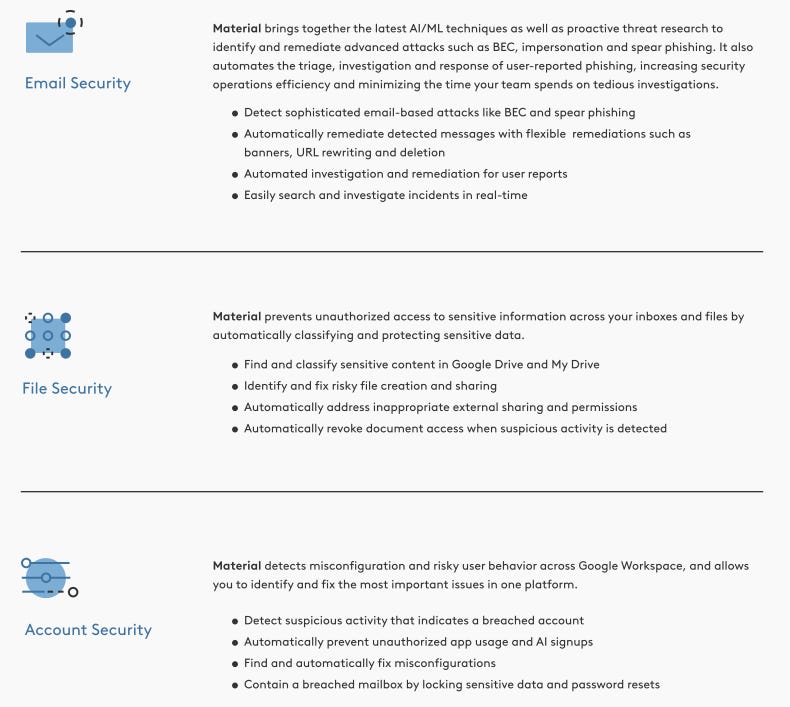
What impressed me most during the demo was how Material has evolved from that initial data protection innovation into a comprehensive cloud workspace security platform. Their approach now spans four interconnected pillars that cover the full lifecycle of workspace threats.
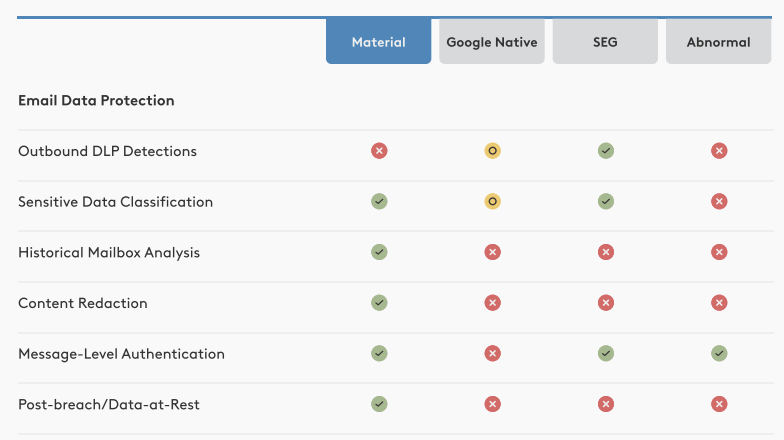
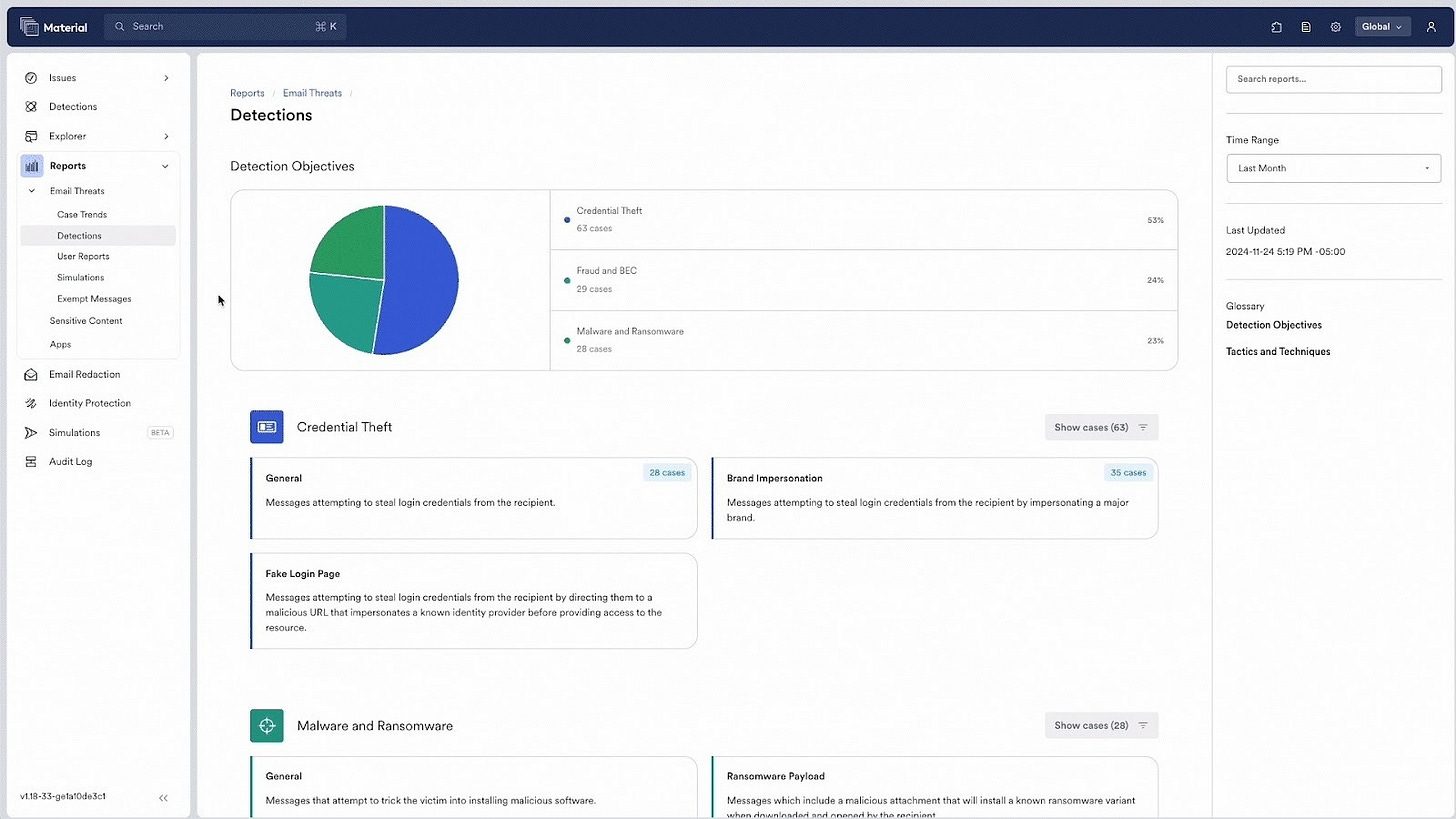
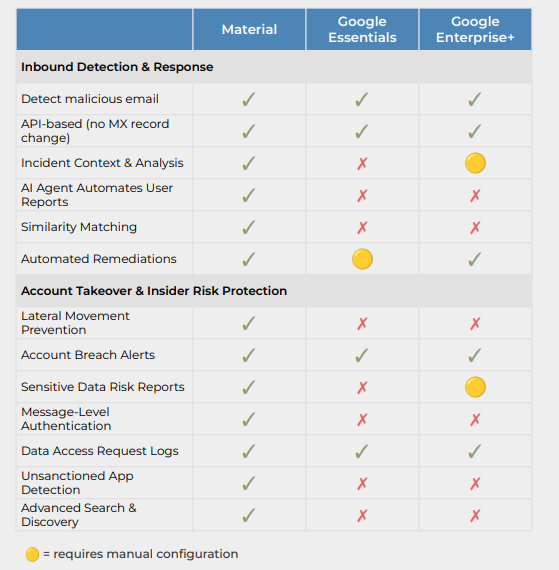
The first is inbound email protection. Material provides API-based, post-delivery detection that catches phishing, BEC, and social engineering attacks that bypass native Google protections. This is the capability that most organizations evaluate first, and it is where Material often runs into competitors like Proofpoint and Abnormal. But as the Material team emphasized during my demo, the phishing detection is the entry point, not the whole story.
The second is the data protection layer I described above. The sensitive data classification, redaction, and MFA step-up that protects data at rest in both email and Google Drive. This is where Material’s differentiation becomes most apparent. No other vendor I’m familiar with approaches the data-at-rest problem with this level of specificity.
The system uses both pre-built and organization-defined DLP classifiers, with the majority of common sensitive data categories like PII, PHI, PCI, and credentials classified out of the box. During the demo, the team walked through how they recommend niche classifications during onboarding for organization-specific items like code names for M&A activities, while deliberately limiting the complexity of customization options to prevent configurations that become unmanageable.
The third pillar is file security for Google Drive. Material scans Drive for sensitive data, tracks sharing permissions, and alerts users about potential oversharing, such as externally sharing an entire customer roster or making a sensitive document publicly accessible. I specifically asked during the demo whether this capability is preventative or detective, and the answer is both.
The system can alert users about oversharing in real time, provide a grace period for the user to respond, and then automatically revoke or downgrade access permissions if the user does not take action. This automated remediation loop addresses one of the biggest operational challenges in data security, which is that detection without response just creates more alert fatigue.
The fourth pillar is account and identity protection. Material uses email behavior as a signal for account compromise, detecting anomalous patterns like suspicious mailbox rule creation, unusual forwarding configurations, and access patterns that deviate from normal behavior.
When a compromise is detected, the platform can automatically contain the account, disable malicious forwarders, pull suspicious messages, and tighten file access. This post-compromise containment capability is critical because most organizations discover account compromises well after the attacker has already accessed sensitive data and established persistence. This approach makes security proactive, rather than just reactive.
What Makes the Approach Unique
Several things stood out to me during the demo and my review of Material’s documentation that I think are worth highlighting.
First, the blast radius framing. Material thinks about security in terms of what an attacker can actually reach and do once they get in, not just whether they can be stopped at the front door.
The “blast radius” of a compromised account encompasses everything that individual has access to, including files in Drive, sensitive emails, shared documents, and connected services. The platform is designed to minimize that blast radius by reducing the amount of accessible sensitive data before a compromise happens and containing the damage when one does.
This framing becomes even more relevant with the rise of tools like Google’s Gemini that can search across an entire workspace. Over-permissive access that was merely a latent risk before becomes an active attack surface when an AI assistant can query across all of it.
Second, the automated remediation paired with detection. One of the most practical problems in security operations is that detection without automated response just adds to the pile of noise and cognitive overload that most teams are dealing with. Material’s approach of pairing every detection with an automated remediation action, whether that is revoking file access after a grace period, pulling a phishing email post-delivery, or disabling a malicious mailbox rule, directly addresses the alert fatigue problem that plagues security teams.
During the demo, the team described customers who run Material entirely “headless,” never logging into the UI. All data flows out via webhooks and subscriptions provide continuous feeds. The SOC can query Material for additional context, triage issues, update remediation status, and trigger Material to take automated action. That level of integration flexibility tells you the platform was designed for real-world operational workflows, not just dashboard demos.
Third, the Google Workspace depth. Material has always been Google-first, built on GCP, leveraging tools like BigQuery and Google’s DLP capabilities. This is not a platform that bolted on Google support as an afterthought to cover both ecosystems.
The team was explicit during the demo that their foundational focus has always been addressing the complexities of Google Workspace, and it shows in the depth of their Drive integration, their understanding of Google-specific sharing models, and their ability to detect workspace-specific attack patterns that generic email security tools miss.
Fourth, the approach to the Secure Email Gateway question. Material is not positioning itself as a direct SEG replacement in the traditional sense. Their framing is more nuanced. Legacy SEGs create costly problems because they miss identity-driven and post-delivery threats, add operational friction through false positives, and duplicate capabilities that cloud-native platforms already provide.
Material’s argument is that the most modern approach keeps native cloud email protections for commodity threats and layers API-based, in-tenant detection and post-delivery remediation on top to handle BEC, internal abuse, account compromise, and the data-at-rest risks that no gateway can address.
The competitive dynamic is interesting. Material often runs into Proofpoint and Abnormal on phishing, but they differentiate through what they describe as the “breadth and depth” of their comprehensive cloud workspace platform that extends well beyond email protection alone.
Material Security recently launched its OAuth Remediation Agent, which gives security teams continuous visibility and automated control over third-party OAuth app connections across Google Workspace. The agent automatically discovers connected apps, kicks off an agentic workflow to research each app, evaluates the permissions and access it holds, and autonomously revokes tokens deemed risky, dormant, malicious, or over-privileged.
With attackers increasingly exploiting trusted app connections, over-permissioned access, and long-lived OAuth tokens to gain a foothold in cloud workspaces, the OAuth Agent extends Material's platform beyond email and file protection into identity and connected app governance across the full cloud workspace.
Why This Matters for the Broader Security Landscape
The email and workspace security category is arguably at an inflection point. The SEG model is aging out, and cloud-native API-based detection has become table stakes. The real differentiation is moving toward platforms that address the full workspace attack surface, including the data-at-rest problem, file sharing risks, account compromise containment, and automated remediation that actually reduces operational burden rather than adding to it. There’s also the factor of AI and Agents, their access to workspaces and data and more to account for.
I have written extensively about the importance of pairing detection with response, of moving beyond static posture toward runtime protection, and of building platforms that cover the full lifecycle rather than just one point in the attack chain. Material’s approach to workspace security reflects those same principles. They are not just asking “can we stop the phishing email?” They are asking “when the account is compromised anyway, how do we minimize the blast radius, protect the sensitive data, contain the damage, and automate the response?” That is a fundamentally different question, and it leads to a fundamentally different architecture and solutions to solve it.
For security leaders evaluating this space, the questions I would ask are direct. Does the solution protect data at rest, or just scan inbound threats? Does it cover Drive and file sharing, or just email? Can it automate remediation, or does it just alert? Does it integrate into your SOC workflow via API, or does it require yet another dashboard? And does it address the blast radius of an account compromise, or does it assume prevention will always succeed?
Material’s answer to each of those questions is what makes their approach worth understanding and is what I found impressive.
The workspace is the treasure chest, it deserves to be protected like one.