The SIEM’s Structural Problem and Why It Matters Now More Than Ever
The detection and response category is facing a challenge that no amount of incremental improvement can solve.
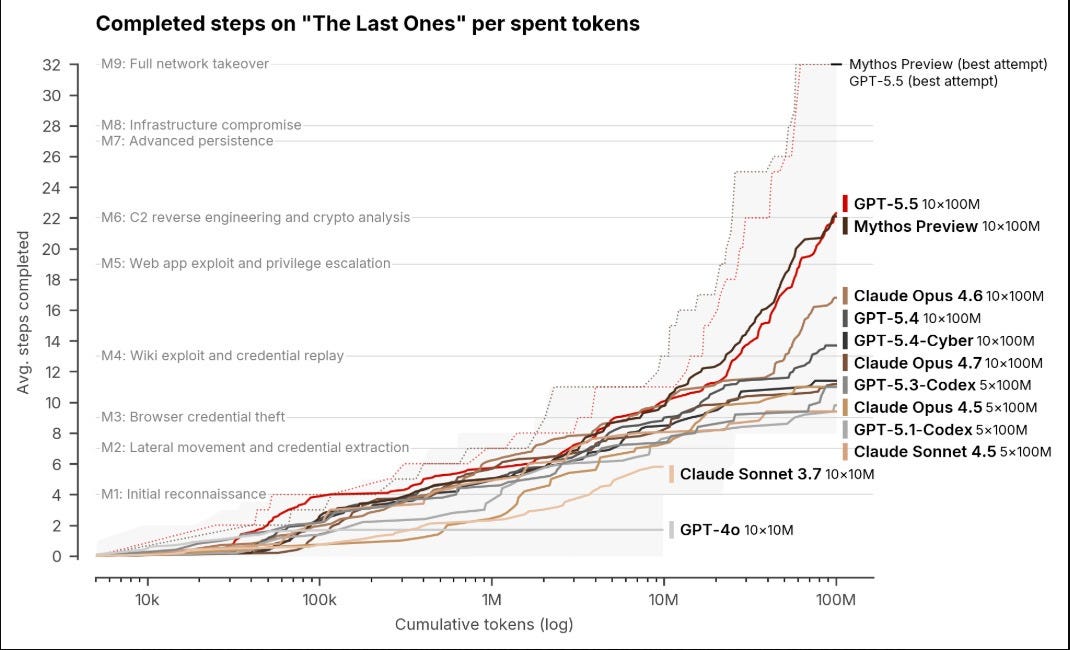
As I covered in The AI Cyber Capability Curve, the UK AI Safety Institute evaluated both Anthropic’s Claude Mythos Preview and OpenAI’s GPT-5.5 and found that both frontier models can autonomously execute multi-stage attack chains spanning the full kill chain, from reconnaissance through lateral movement to objective completion.
Two different models from two different labs, both independently demonstrating capabilities that compress what used to take human attackers weeks into minutes.
This isn’t a marginal increase in attacker sophistication, it’s a structural change in how attacks are composed and executed.
When offensive tools can autonomously chain together reconnaissance, exploitation, lateral movement, and data exfiltration in a single session, the detection system on the receiving end needs to reason about multi-step attack narratives in real time rather than matching individual events against static rule sets.
Pair that with what I documented in The Attack Surface Exponential, where GitHub is on pace for 14 billion commits in 2026 (14x year-over-year) and FIRST projects approximately 59,000 new CVEs this year, and the picture becomes clear. The volume, velocity, and autonomy of attacks have fundamentally outpaced the architecture that most organizations rely on to detect them.
This is the context in which I sat down with Resilient Cyber’s partner, Artemis Security’s Co-Founder Shachar Hirshberg to see what they’ve built and understand why they believe the detection and response category needs to be rebuilt from the ground up.
Why Legacy Architecture Can’t Adapt
The incumbents in the SIEM market aren’t failing because they lack talent or investment. They’re failing because the architectural decisions they made a decade ago have compounded into structural limitations that can’t be patched with an AI feature bolted onto an existing codebase.
Traditional SIEMs ingest raw logs, apply static detection rules, and produce alerts. The rules are generic, applied uniformly across organizations regardless of how different their environments, business logic, and risk profiles actually are.
When a new attack technique emerges, someone has to write a rule for it. When that rule generates false positives in a specific environment, someone has to tune it. When the alert fires, someone has to investigate it manually, pulling context from multiple systems to determine whether the alert represents a real threat or noise.
Every step in that chain is a human bottleneck, and every bottleneck gets worse as the volume and velocity of both data and attacks increase. SOC teams receive an average of 11,000 alerts per day, while only 22 per analyst warrant genuine investigation.
The result is the alert fatigue problem the industry has been complaining about for years, where 40% of alerts are never investigated and 61% of teams admit to ignoring alerts that later proved critical. Legacy SIEM architecture was built for a world where threats moved at human speed and followed patterns that static rules could anticipate.
When attackers are autonomous AI agents executing novel multi-step attack chains that no rule writer has seen before, pattern-matching against known signatures isn’t a detection strategy, it’s a rearview mirror.
What Artemis Security Built and Why
Shachar’s background is relevant to understanding why Artemis Security takes a fundamentally different architectural approach. He led AWS GuardDuty and was a leader at Demisto through its acquisition by Palo Alto Networks, which means he built the previous generation of detection and response tooling and understands its limitations from the inside.
His co-founder Dan Shiebler brings a different but equally critical perspective. Dan spent the last decade building large-scale AI systems and, most recently, led ML and AI at Abnormal AI, where he applied research from his PhD in machine learning at Oxford to develop AI-powered detection systems powering one of the fastest-growing email security platforms in the market.
A lot of the core architectural ideas behind Artemis are built on work he’s been iterating on for years. At Twitter, he worked on behavioral modeling systems representing how millions of users interacted with the platform. At Abnormal, similar concepts helped model how organizations communicate and identify behavior that didn’t belong.
Together they decided the detection and response problem couldn’t be solved by iterating on the existing SIEM architecture. It required starting from scratch with a codebase Shachar describes as “built by agents for agents,” designed from the ground up for an agentic AI architecture.
Artemis is also one of a select few cybersecurity companies working in deep collaboration with Anthropic, integrating Claude’s reasoning capabilities directly into the platform across multiple model tiers.
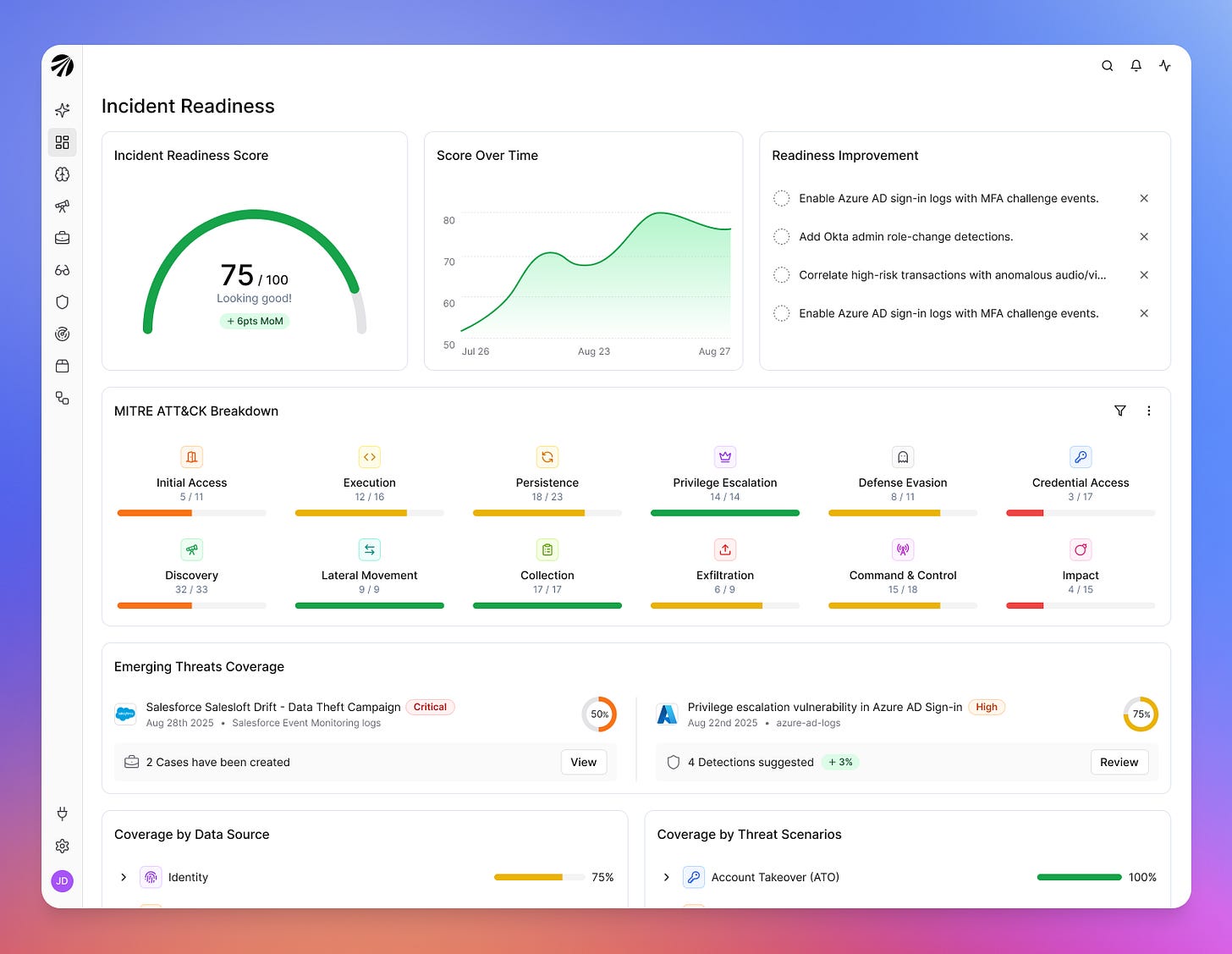
Three Layers of Detection
The most significant architectural difference I observed in my conversation and demo with Shachar is how Artemis Security handles detection. I’ve seen a lot of vendors claim “AI-powered detection” over the past 18 months, and most of them are doing the same thing they’ve always done, matching rules against logs, with a summarization layer on top that generates a paragraph of text instead of a raw alert.
Artemis runs three distinct detection layers that work together to reduce noise and increase signal quality before anything reaches an analyst, and the architecture is genuinely different from what I’ve seen elsewhere.
The first layer covers base core detections aligned to frameworks like MITRE ATT&CK, the kind of coverage every organization needs across connected data sources. This is table stakes, and every serious platform provides it.
The second layer is where the differentiation begins. Artemis Security generates adaptive detections that are built specifically for each customer’s environment by analyzing their telemetry and business context.
The platform creates, measures, tunes, and maintains them autonomously, which is why Anthropic highlighted Artemis in a case study that report a 90% increase in detection coverage with environment-specific detections auto-built and tuned from day one.
Even within a single enterprise, different business units get distinct detection logic because their infrastructure and operational patterns differ. This is the kind of environment-specific detection engineering that most organizations either can’t staff for or can’t scale, and it addresses a problem I’ve seen repeatedly across the industry.
Generic detection rules treat every organization as if it has the same infrastructure, the same business logic, and the same risk profile, which is why they generate so much noise. Per-environment adaptive detection is what detection engineering should have always been, but the cost of doing it manually made it impractical until the underlying detection engine could generate and maintain the rules autonomously.
The third layer is behavioral analytics, and this is where I suspect Dan’s research background shows up most directly in the product. The platform maps expected activity patterns against actual behavior across all connected data sources, building behavioral baselines from the customer’s own data rather than applying generic heuristics.
When you combine environment-specific adaptive detections with behavioral baselines built from the customer’s actual operational patterns, the detection surface becomes fundamentally different from what a generic rule set can achieve.
As Shachar put it during our conversation, the fundamental advantage defenders have is knowing their own environment better than any external attacker does, and Artemis Security is designed to help defenders actually leverage that advantage rather than let it go to waste.
Having evaluated a lot of security products that claim to offer “contextual” or “environment-aware” detection, I think Shachar is right about the structural insight even if most of the market hasn’t operationalized it yet. The defenders’ asymmetric advantage is environmental knowledge, and most detection tools throw that advantage away by applying the same rules everywhere.
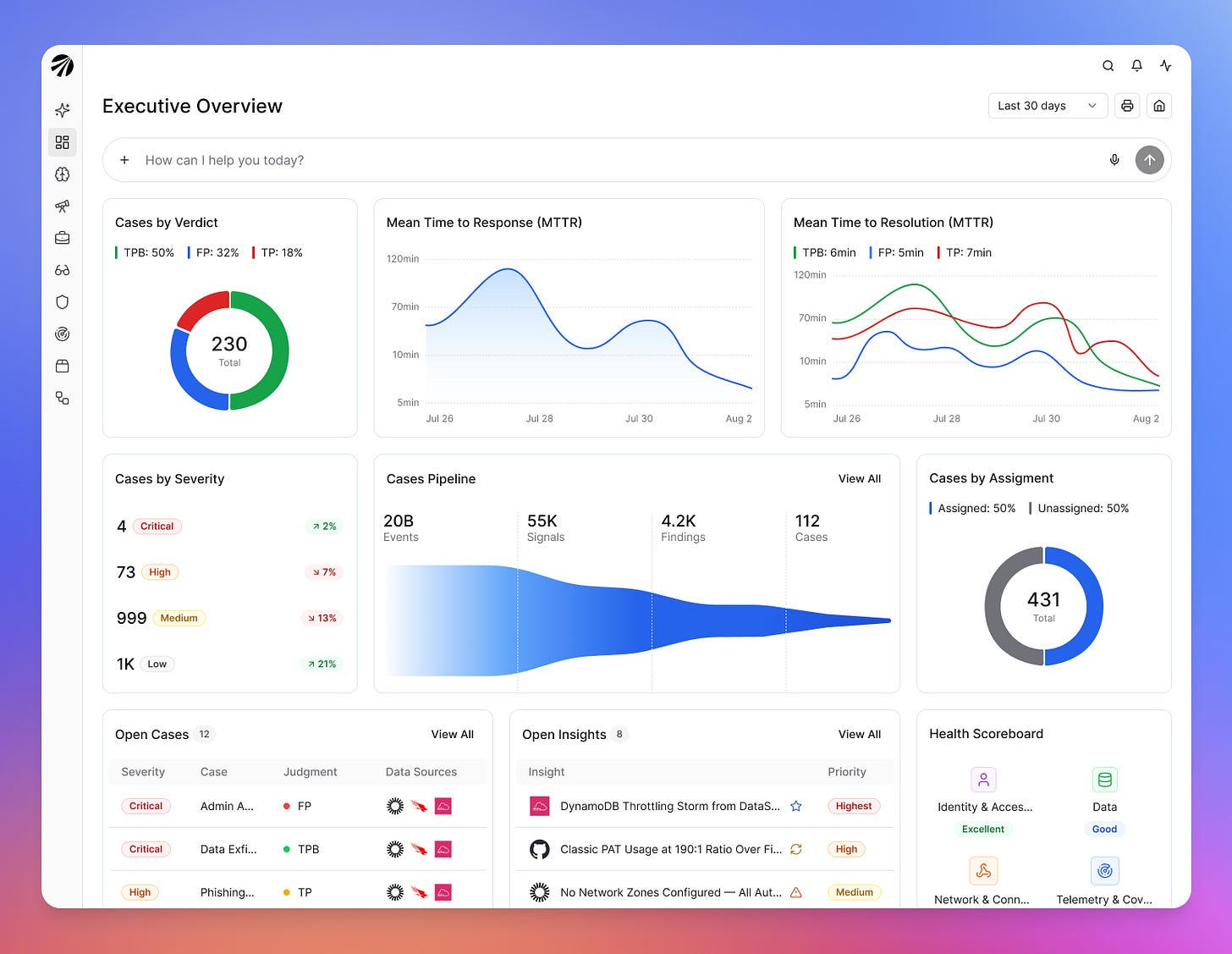
From Signals to Cases
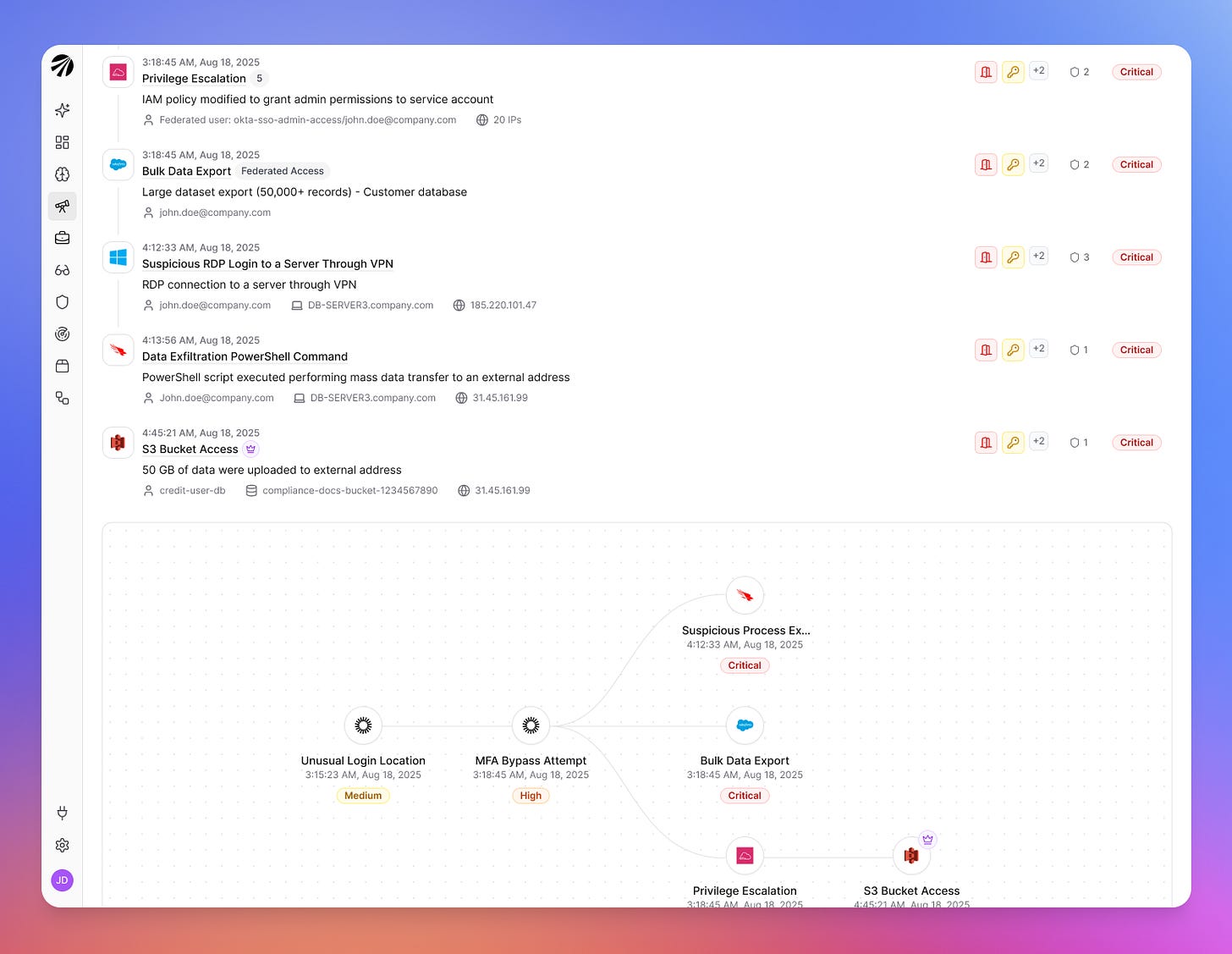
The detection layers produce what Artemis Security calls “signals,” which are then distilled into “findings” using multiple analytical models, but the real differentiator is what happens next, and it’s where the architectural bet on agentic AI pays off most visibly.
An agentic investigation layer takes those findings and builds “cases” that provide a fully contextualized narrative of an attack. When a detection fires, Claude-powered investigation agents take over, formulating hypotheses, querying across log sources, correlating signals, and producing reports with severity assessments and clear chains of reasoning.
This is the step that traditional SIEMs skip entirely, leaving the analyst to manually correlate alerts across data sources, build timelines, and determine whether related signals represent a coordinated attack or unrelated noise.
During the demo, I watched this pipeline operate on real telemetry. Thousands of signals were processed, correlated across cloud, identity provider, EDR, and SaaS log sources, and assembled into a handful of cases that each told a complete story. The output wasn’t a list of alerts ranked by severity.
It was an attack narrative with a timeline, affected entities, the relationship between events, and a judgment on the severity and confidence of the finding. The graph technology underlying the platform models all relationships among assets, entities, AI agents, and users within the customer’s organization, which is what makes the correlation possible at that level of depth.
For a SOC analyst, the difference between receiving 500 alerts that need individual investigation and receiving 5 cases that each present a complete attack story with context and judgment is the difference between drowning and actually doing security work.
I’ve heard similar claims from other vendors, but the demo I saw showed the full pipeline operating end-to-end on real data rather than a curated demo scenario, and the investigation output included cited evidence for every conclusion rather than a vague AI summary.
The cases also come with dynamically generated response guidance and one-click actions, allowing the analyst, or Artemis, to take action and reduce the time the attack can impact their organization.
The Anthropic case study reports a 96% reduction in mean time to resolution, with structured, evidence-cited attack reports produced in under five minutes compared to multi-hour manual investigations, that tracks with the architecture. When you eliminate the manual correlation and investigation steps that consume the bulk of analyst time, the response timeline compresses dramatically.
Data Strategy and Cost Savings
One of the persistent structural problems with traditional SIEMs is the incentive misalignment between detection coverage and cost. The more logs you ingest, the higher your bill, which creates a perverse dynamic where organizations make security-critical decisions about what data to collect based on licensing costs rather than risk coverage.
I’ve written about this pattern across other domains, where the incentive structure produces behavior that looks irrational from the outside but is perfectly rational given the economic constraints. A CISO who chooses not to ingest EDR telemetry because it would double the SIEM bill isn’t being negligent. They’re making a cost-benefit tradeoff that the pricing model forces them into, and the vendor benefits from the dynamic because it creates upsell pressure.
Artemis Security approaches data differently through what they call “hybrid analytics.” Core logs are ingested directly, while the rest of the raw telemetry (EDR data, for example) is brought in on demand through a federated approach, pulling from S3 buckets, Snowflake instances, or EDR systems only when the investigation requires it.
This matters because it means organizations can connect all their data sources without worrying about cost blowout from ingesting petabytes of EDR telemetry that they might never need. The platform currently analyzes approximately 15 petabytes of data daily across their customer base, and when the investigation layer needs EDR context for a specific case, it queries the data where it lives rather than requiring it to be pre-ingested and stored.
A solution that pays for itself
The environment intelligence capability extends the cost savings further. The platform performs dynamic analysis of customer logs to surface posture and cost insights, and Shachar mentioned that this capability alone has saved customers over $5 million, primarily by identifying opportunities to optimize cloud spend.
For CISOs who are constantly defending their budget, a security platform that pays for itself through infrastructure optimization while simultaneously improving detection and response is a genuinely compelling value proposition, and it reframes the conversation from “what does security cost” to “what does security save”, while still playing a key part in mitigating organizational risks.
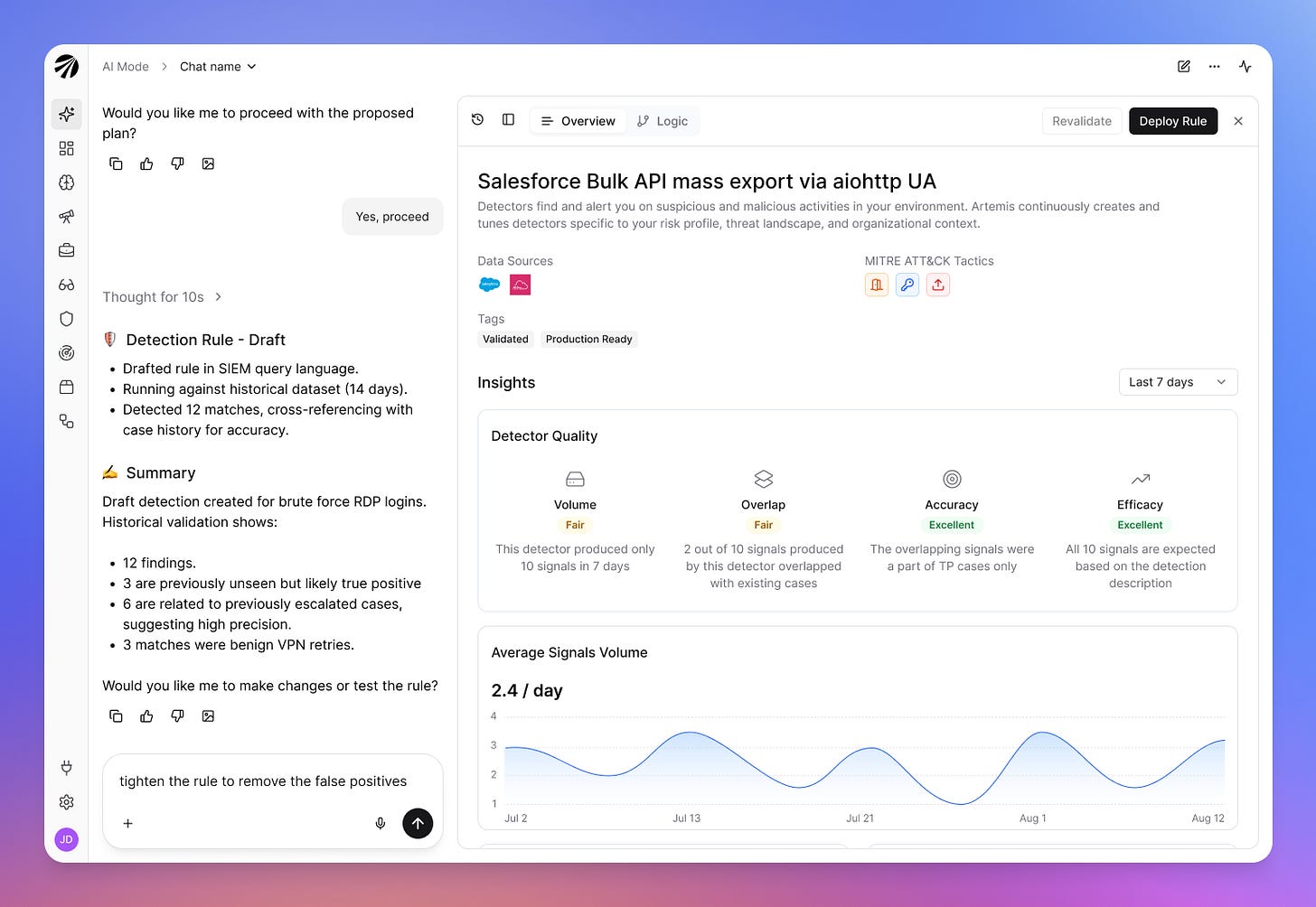
AI Mode and the Talent Multiplier
The AI Mode capability addresses a problem that every security leader I know is wrestling with, and it’s one I think about frequently when I look at the gap between what organizations need their security teams to do and what those teams can actually execute. The cybersecurity talent shortage isn’t new, but the gap keeps widening because the complexity of what SOC analysts need to investigate grows faster than training programs can develop expertise.
Traditional security operations require deep expertise in query languages, detection engineering, and forensic investigation, skills that take years to develop and that most organizations don’t have enough of. Artemis Security’s AI Mode allows analysts to create detections, run threat hunts, and investigate activity using natural language. This works because the platform already understands the customer’s organization, assets, and telemetry, so a few words from the analyst trigger dozens of underlying queries, with the platform collecting and synthesizing the results into actionable output.
During the demo, I saw how this effectively allows a Tier 1 analyst to perform tasks that would traditionally require Tier 3 expertise. What struck me about this wasn’t the natural language interface itself, which is increasingly common, but the depth of organizational context behind it.
Most “AI copilot” products I’ve evaluated translate natural language into queries against whatever data happens to be in the SIEM. Artemis Security’s AI Mode translates natural language into investigations grounded in the platform’s understanding of the customer’s specific environment, assets, and behavioral baselines, which produces fundamentally different output because the context is richer.
This doesn’t replace skilled analysts, it amplifies them and allows less experienced team members to contribute at a higher level, which is exactly what security teams need when they can’t hire fast enough or have budgetary constraints to match the workload.
The automated threat hunting capability operationalizes this further. The platform subscribes to approximately 50 threat intelligence feeds and proactively hunts for indicators relevant to the customer’s specific environment. This turns threat intelligence from a passive feed that analysts rarely have time to act on into an active detection mechanism that runs continuously without human intervention.
The Timing and Market Context
Artemis Security emerged from stealth with $70 million in combined seed and Series A funding (the Series A led by Felicis), has been in production for less than six months, and has already deployed with several Fortune 500 companies and leaders in banking and technology.
The speed of customer adoption says something about market readiness. Organizations aren’t just interested in incremental improvements to their existing SIEM. They’re actively looking for a fundamentally different architecture because the existing one can’t keep pace with how attacks are evolving.
The timing connects directly to the broader trends I’ve been covering. As I wrote in The AI Cyber Capability Curve, every model generation pushes offensive capabilities further along the kill chain, and each generation arrives faster than the last.
The gap between discovery and exploitation has collapsed from years to hours, and open-weight models costing pennies per million tokens can surface the same classes of bugs that frontier models find. Detection and response systems designed for human-speed attacks simply cannot match adversaries that operate at machine speed and execute complete attack chains autonomously.
What struck me in my conversation with Shachar wasn’t the feature set in isolation, though the capabilities are impressive. It was the cohesiveness of the architectural vision and how clearly it reflects both founders’ prior experience.
Shachar built the previous generation of detection tooling and saw where it broke. Dan spent a decade developing the behavioral modeling and AI-powered detection approaches that could fix it.
Every component, from the three detection layers to the agentic investigation pipeline to the hybrid data strategy to the natural language interface, is designed around a single insight. The detection and response problem isn’t a data problem or a rules problem or a staffing problem in isolation.
It’s all of those problems compounding against each other in a system that was never designed for the volume, velocity, and complexity of modern attacks. You can’t fix that by adding features to an architecture that was built for a different era. You have to rebuild the architecture with the current threat model as the design constraint.
The SIEM category has been ripe for disruption for years, but the competitive moats of data ingest and enterprise distribution protected incumbents from having to fundamentally rethink their approach.
AI-accelerated attacks have changed that calculus. When threats move at machine speed and execute autonomous multi-step attack chains, the detection and response system needs to operate at the same speed with the same depth of contextual understanding.
Artemis Security is building for that reality rather than iterating on the architecture that couldn’t keep pace with the previous one.