The Firewall Evolved, and It Was About Time
A look at what a modern hybrid mesh firewalls looks like in practice
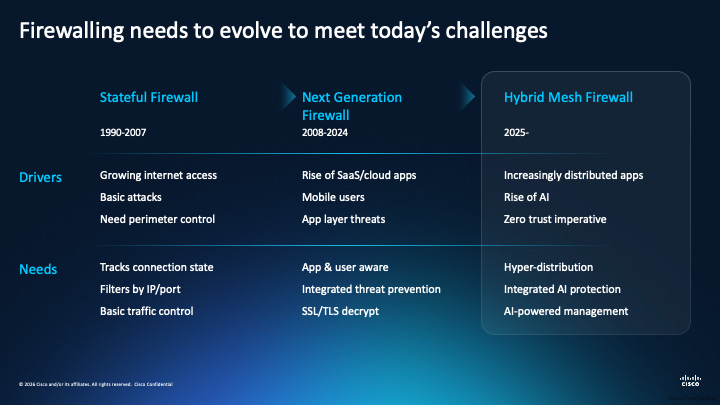
Having spent time as a security engineer, architect, and CISO, I’ve watched the firewall conversation cycle through the same pattern for over a decade. Someone declares the firewall dead, vendors push back with a new appliance that adds a few features and the industry moves on.
Meanwhile, the environments we’re actually responsible for securing have fundamentally changed while the enforcement model stayed frozen in a perimeter-centric architecture that stopped reflecting reality years ago.
The problem was never the firewall as a concept.
Evaluating traffic against policy and making allow or deny decisions is as foundational to network security as authentication is to identity. The problem was that the implementation stayed anchored to a model where you could draw a line around your environment and put enforcement at the boundary.
That model assumed your workloads lived in data centers you controlled, your applications ran on infrastructure you owned, and your users accessed everything from managed endpoints inside a corporate network. None of those assumptions hold for most enterprises today, and if we’re being honest, most would agree they haven’t for a while.
Gartner formalized this reality in January 2024 when they published the Market Guide for Hybrid Mesh Firewall Platforms, followed by the inaugural Magic Quadrant for Hybrid Mesh Firewall in August 2025.
For those unfamiliar, Gartner defines a hybrid-mesh firewall (HMF) as a multi-deployment firewall that includes hardware, virtual appliance, and cloud-based options, all controlled via a unified cloud-based management plane.
But what does that actually look like in practice, from the perspective of a vendor’s offering and capabilities? I’ll be using Resilient Cyber’s partner Cisco as an example in this piece to walk through exactly that.
Cisco’s Hybrid Mesh Firewall is their implementation of this model, and having followed their approach through multiple analyst recognitions including being named a Leader in the Forrester Wave for Enterprise Firewall Solutions and a Leader in the IDC MarketScape for Enterprise Hybrid Firewall, the way they’ve assembled the platform reflects a genuine understanding of the operational problems practitioners face when trying to enforce consistent policy across environments that resist consistency.
The Operational Pain Practitioners Know
Anyone who has actually operated a security program across hybrid environments understands the pain that the hybrid mesh firewall model is designed to solve.
You have hardware appliances in the data center running one policy set. You have virtual appliances in AWS and Azure running different policy sets managed through different consoles. You have cloud-native security groups and network ACLs that technically enforce access control but are managed by cloud engineering teams who may or may not coordinate with the security organization. You might have a SASE or SSE solution handling remote user traffic with its own policy engine, and somewhere in a spreadsheet or a wiki, someone has documented the “intended” security architecture that none of these individual enforcement points fully reflects.
The result is what every practitioner in this space has lived through. Policy drift between what you think is enforced and what actually is enforced. Blind spots in encrypted traffic that you can’t inspect without deploying additional infrastructure and accepting the latency, certificate management complexity, and privacy implications that come with it.
Lateral movement paths that exist because microsegmentation was planned but never fully implemented because the operational overhead of manually defining every permitted flow was too high for the team to sustain, and incident response scenarios where correlating activity across five different management consoles turns a 30-minute investigation into a half-day exercise.
This isn’t a failure of any single product, it’s a failure of the architectural model that treated each environment as a separate security domain requiring its own enforcement stack, its own management plane, and its own policy language. The hybrid mesh firewall concept is fundamentally about collapsing those silos into a single policy fabric that spans every environment, every form factor, and every enforcement point from a unified control plane.
What Cisco Assembled
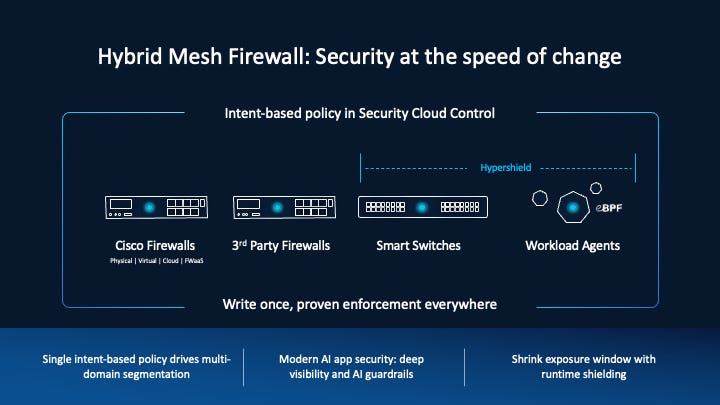
Cisco’s approach to the hybrid mesh firewall isn’t a single product launch. It’s an integration of a portfolio of capabilities into a cohesive architecture that reflects how enterprises actually need to enforce policy across heterogeneous environments.
The components include Cisco Secure Firewall for hardware and virtual appliance enforcement, , Multicloud Defense for cloud-native firewall orchestration across AWS, Azure, GCP, and Oracle OCI, Secure Workload for zero-trust microsegmentation, and the new Cisco Smart Switch with security powered by Hypershield technology. All of it is managed through Security Cloud Control, a unified orchestration platform that provides a single management plane across the entire enforcement fabric.
AI and machine learning (ML) capabilities run throughout capabilities in the platform. For example at the edge, Encrypted Visibility Engine uses ML to classify threats in encrypted traffic without requiring full TLS decryption, which addresses an operational headache that has plagued security teams for years.
Decrypting traffic at scale introduces latency, certificate management complexity, and privacy concerns that many organizations simply can’t accept across all traffic flows. Being able to classify encrypted traffic through ML-based fingerprinting is a meaningful operational improvement for teams that have been forced to choose between visibility and performance.
Snort ML, another Cisco firewall innovation, complements traditional signature-based detection to recognize new or previously unknown variants by detecting exploit behavior at the vulnerability-class level rather than only matching a fixed signature.
And Secure Workload uses unsupervised machine learning to automatically discover application communication patterns and recommend microsegmentation policies tailored to the environment. This is exactly the kind of automation that could have prevented the microsegmentation initiatives I’ve seen stall at 30% coverage because the team ran out of capacity to manually define policies.
Microsegmentation is another example of a security best practice that is often more talked about than implemented due to the level of effort required, so seeing Cisco utilizing ML to accelerate and automate these capabilities in action is pretty cool.
The Zero Trust Connection
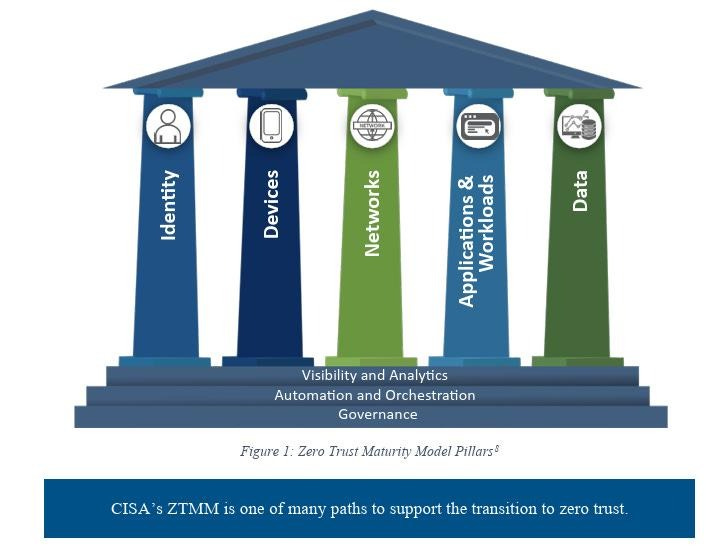
You can’t discuss network and workload security without discussing zero trust principles and having spent a good amount of my career in the public sector, CISA’s ZTMM is a resource I often tie back to.
CISA’s Zero Trust Maturity Model v2.0, published in April 2023, organizes zero trust implementation across five pillars (Identity, Devices, Network, Applications and Workloads, and Data) with three cross-cutting capabilities (Visibility and Analytics, Automation and Orchestration, and Governance) spanning all five. The model defines four maturity stages from Traditional through Optimal, giving organizations a practical framework for assessing their current posture and mapping a path forward.
While the Network pillar is where the hybrid mesh firewall concept maps most directly, the more interesting alignment is with the cross-cutting capabilities. Visibility and Analytics demands comprehensive monitoring and telemetry across all enforcement points, which is exactly what a unified management plane provides when you aren’t stitching together visibility from five different consoles.
Automation and Orchestration calls for automated policy enforcement and reduced manual intervention, which aligns with AI-driven policy generation, , and centralized orchestration from a single control plane.
Governance requires consistent policy management, compliance verification, and continuous improvement, which a single policy fabric across heterogeneous environments makes operationally achievable in a way that fragmented enforcement stacks never could.
Again, many of these were largely conceptual among the security community, now we have products and capabilities to make them real-world implementations. The maturity progression from Traditional to Optimal in CISA’s model essentially describes the journey from perimeter-based firewalls to hybrid mesh firewall architecture.
At the Traditional stage, organizations rely on static, perimeter-focused enforcement with manual processes. At the Optimal stage, they have fully distributed enforcement with continuous adaptation, automated policy generation, and real-time threat response. Hybrid mesh firewall is the infrastructure that makes the Optimal stage practically achievable rather than aspirationally described in a maturity model document that nobody knows how to operationalize.
The point that resonates from a practitioner perspective is that CISA’s model doesn’t tell you to abandon firewalls, it tells you to evolve them. Zero trust doesn’t mean “trust nothing and enforce nothing.” It means verify everything and enforce everywhere.
The firewall as a concept, an enforcement point that evaluates traffic against policy and makes allow or deny decisions, is more relevant in a zero trust architecture than it was in a perimeter-based one. You just need more enforcement points, in more places, managed consistently, and informed by better intelligence than static rule sets can provide.
I previously was involved in this sort of Zero Trust work at large complex Federal agencies and due to the traditional level of manual effort required, they often fell short of the ZT goals and aspirations.
Cloud, SaaS, and the Hybrid Reality
The environments most enterprises operate in today would be unrecognizable compared to what most of us were securing a decade ago. Production workloads run across multiple public clouds. Business-critical applications are SaaS platforms that the organization doesn’t control and can’t deploy traditional enforcement points in front of in any meaningful sense and APIs connect everything to everything.
Containers spin up and down in minutes. Serverless functions execute with no persistent infrastructure to attach a security policy to, and through all of this, the data that matters, customer records, intellectual property, financial transactions, flows between environments that were never designed with consistent security enforcement in mind.
The hybrid mesh firewall model addresses this by treating enforcement as distributed and environment-aware rather than centralized and location-bound which is particularly key for multi-cloud and hybrid cloud environments.
For SaaS environments where inline enforcement isn’t feasible, the combination of identity-aware policy, encrypted traffic analysis, and API-level controls provides visibility and governance that the perimeter model simply couldn’t offer. You can’t put a firewall in front of Salesforce in any traditional sense, but you can enforce policy on how users, workloads, and increasingly agents interact with those platforms through identity-driven controls and traffic analysis operating at the mesh layer.
The gap between what security teams want to enforce and what they can operationally sustain has been the single biggest barrier to consistent policy enforcement across hybrid environments, and closing that gap through automation and managed services is how you move from aspirational architecture diagrams to actual deployed enforcement.
The AI and Agentic Dimension
The firewall conversation in 2026 can’t ignore the fact that AI workloads, and increasingly AI agents, are creating an entirely new attack surface and security requirements. AI agents make API calls at machine speed, invoke tools dynamically based on runtime reasoning, chain interactions across multiple services and environments, and operate with a degree of autonomy that traditional security tools, built around predictable human-initiated actions, can’t adequately govern.
Cisco has explicitly positioned Hybrid Mesh Firewall as part of their security strategy for the agentic AI era, integrating security for AI workloads and the development and deployment of AI models and applications.
Traditional firewall rules that allow or deny based on source, destination, and port are insufficient when the same agent might make dozens of different API calls in a single task execution, each to a different service, each with different security implications, and the sequence isn’t predictable at policy-definition time.
This is where Isovalent’s eBPF-based, kernel enforcement becomes directly relevant for AI workloads running in Kubernetes environments.
To secure the development and deployment of AI models and applications, Cisco AI Defense is integrated into the Hybrid Mesh Firewall architecture, providing AI discovery, validation, supply chain protection, and runtime guardrails.
As I’ve covered across multiple pieces on agentic AI security, including the distinction between soft guardrails and hard boundaries, system prompts and model-level instructions are probabilistic controls that agents can and do override.
Hard boundaries enforced at the infrastructure layer, where the enforcement mechanism operates below the model and outside its reasoning process, are the only reliable way to prevent autonomous agents from taking actions that exceed their intended scope. Distributed, kernel-level enforcement through eBPF is exactly that kind of hard boundary applied at the network and workload layer.
The Practitioner’s Perspective
Having operated across the full spectrum of security roles, what I value most in any security platform is whether it makes the security team’s job operationally achievable rather than theoretically possible. The gap between those two things is where most security programs fail, not because the team doesn’t understand what they should do, but because the tooling makes doing it so operationally painful that shortcuts become the norm and “good enough” becomes the standard.
The hybrid mesh firewall model, and Cisco’s implementation of it, closes several of those gaps. Unified management across heterogeneous environments means fewer consoles, fewer opportunities for policy drift, and faster incident investigation.
AI-driven policy generation means microsegmentation initiatives that actually reach full deployment instead of stalling because the team ran out of capacity to manually define permitted flows. Encrypted traffic analysis without full decryption means visibility into the vast majority of enterprise traffic without the operational overhead and privacy implications of TLS interception at scale, and distributed enforcement that operates at the kernel level, at the cloud boundary, and at the data center perimeter simultaneously means that zero trust becomes something you implement rather than something you describe in a strategy document that collects dust.
The perimeter “only” approach to firewalls is not enough, and the days of static, siloed security tools are numbered.
The replacement model is here now, and it looks like distributed enforcement managed from a unified control plane, informed by AI, and deployed wherever workloads actually run rather than wherever the network boundary happened to be drawn a decade ago.
For practitioners who have spent careers trying to enforce consistent security policy across environments that resist consistency at every turn, that isn’t just a product evolution, it’s the architectural shift that makes the job possible.