Innovating Cybersecurity Investigations
A look at Binalyze 2025 "State of Cybersecurity Investigations" Report
The scale, pace, and impact of cybersecurity incidents can’t be described as anything but overwhelming. From impacting critical infrastructure, military and financial systems, and disrupting national activities that citizens depend on, cybersecurity attacks are pervasive.
Attackers continue to innovate, seeking ways to maintain leverage over victims, expand their impact through supply chains, and demand compensation for reprieve. AI is poised to exacerbate the problems, with researchers demonstrating how AI can be used to create exploits in minutes and leading model providers detailing how attackers are conducting cyber espionage with their platforms.
Are we in the golden age for attackers? It can certainly feel like it sometimes, as their activities grow in pace and impact, and we become desensitized and numb due to the constant headlines of incidents.
That’s why I am looking forward to digging into Binalyze’s State of Cybersecurity Investigations Report. Not only does it highlight key challenges, such as the growing scale and impact of cyber incidents, but it also points out glaring gaps in crisis management, digital forensics, and the way organizations respond to incidents when they do occur, which, as we all know, they inevitably will.
The report is full of key insights, many of which are quantified in both dollar value and organizational impact, making the findings actionable for security leaders as they seek to optimize their security programs and investigative activities, as well as justify additional investments to leadership when needed.
What also makes Binalyze’s report unique is that it focuses on Cyber Scene Investigations (CSI), along with the importance of rapid forensic response activities in identifying ongoing cyber incidents and mitigating their subsequent impact on organizations.
The report involves 200 U.S. CISOs, providing real-world insights into cybersecurity preparedness, digital forensics, and the inner workings, gaps, and challenges faced by existing security leaders.
So, let’s take a look at some of the findings and their implications for security leaders.
You can grab a FREE copy of the Binalyze 2025 State of Cybersecurity Investigations Report below.
Key Takeaways
With the intro out of the way, let’s get into some of the findings from the State of Cybersecurity Investigations Report. I always like to start with the bottom line up front (BLUF), which Binalyze provides in the below snapshot:
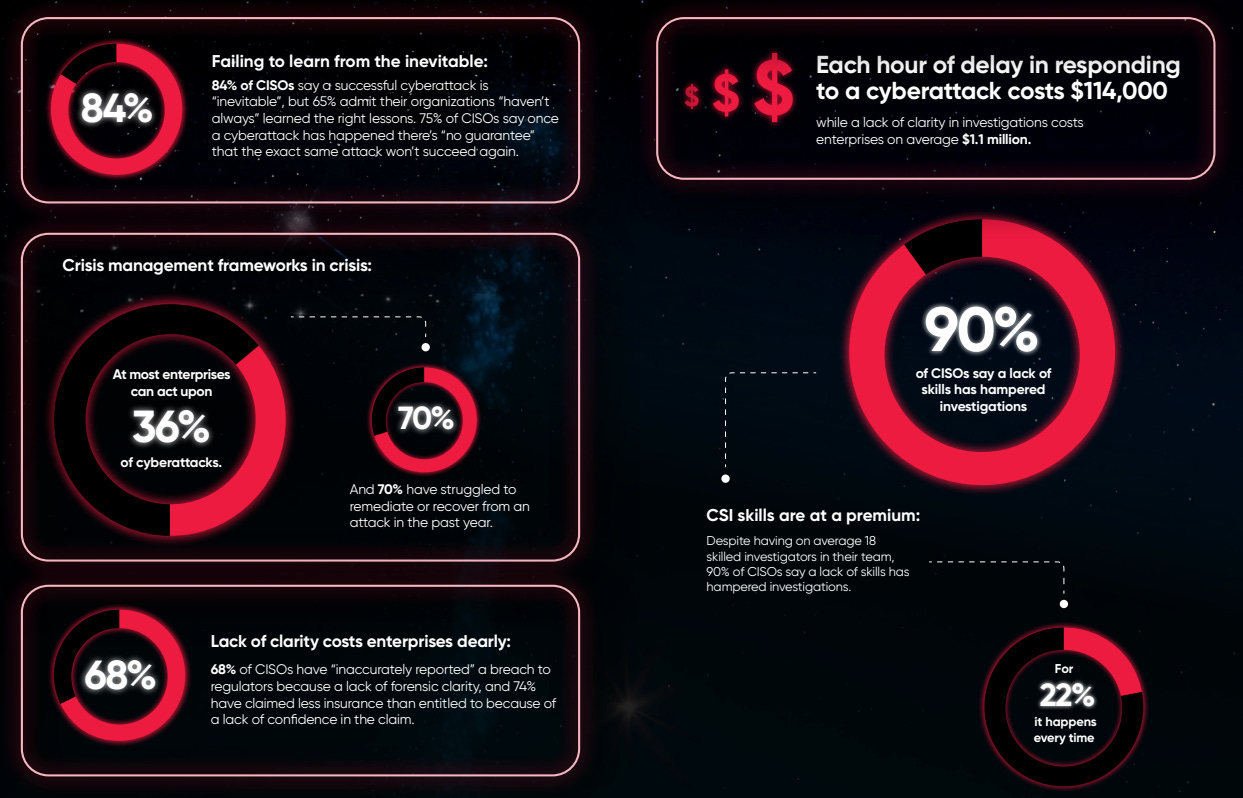
Here we see some pretty damning statistics emerging from the survey. These include the fact that organizations simply aren’t learning from incidents, indicating they aren’t leveraging the painful experience to make organizational improvements to either eliminate future risks or at least decrease their impact.
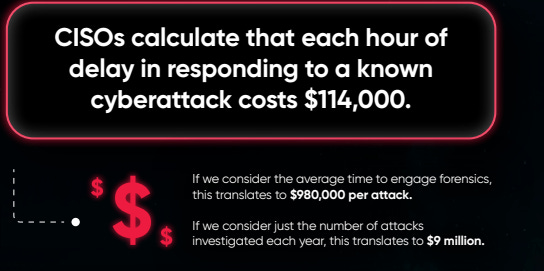
Additionally, the majority of organizations lack a coherent crisis management framework and are struggling to recover from incidents long after the initial pain subsides. Worse yet, most CISOs admitted that their organizations have inefficient forensic capabilities and can’t even properly report breaches when they do occur. These inefficiencies manifest in dollars, as every single hour of delay in responding to cyber incidents costs organizations $114,000. This cost is magnified at the incident level, culminating in an average of $1.1 million due to a lack of clarity during incidents. Binalyze estimated that, overall, this is a $48.1 billion problem, a staggering figure that represents the culmination of inefficiencies across cyber investigations.
Cybersecurity often has a reputation as a cost center, and as you see here. Throughout the rest of this deep dive, we are living up to that reputation, costing our organizations even more due to duplicative and disjointed tooling as well as inefficiencies in our forensics and investigative activities. These challenges also have ties to the workforce, with nearly all (90%) of CISOs admitting that a lack of cyber scene investigation skills hinders their investigative activities, despite having 18~ skilled investigators on their teams.
“Golden Age”?
Binalyze’s report asks an interesting question, in the form of “Are we in the golden age for attackers?” There’s certainly a case to be made, as we discussed above, given that cyber incidents are growing in scale, impact, and reach, affecting all aspects of society. Additionally, attackers are using AI to accelerate and amplify their activities, with the latest example being the reported use of Claude and Agents by a nation-state actor for cyber espionage activities by leading model provider Anthropic. On even more alarming, in mid-November,
Anthropic released a report titled “Disrupting the first reported AI-orchestrated cyber espionage campaign”, where they detailed how a malicious actor targeted 30~ organizations using Anthropic’s AI platform and agents to automate 80-90% of their attack lifecycle from reconn through data exfiltration. The incident sent shockwaves through the cybersecurity community.
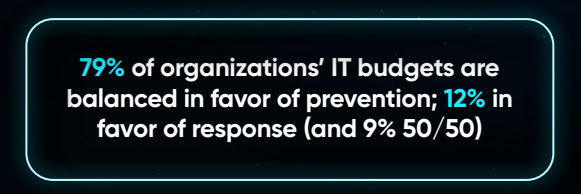
One could ask if we’re over-optimizing our cybersecurity spend on prevention, and still seeing a growth in incidents and impacts despite this prioritization on prevention.
As seen above, the majority of IT budgetary spend on security focuses on prevention, with Binalyze finding that budgets, on average, have a 2:1 ratio in favor of prevention.
While some adages apply, such as “an ounce of prevention is worth a pound of cure”, the reality is that we’re not doing so hot when it comes to effective prevention, despite the significant financial prioritization. Ironically, we’re struggling terribly with response, given merit to another adage such as “prevention is ideal, but detection and response is a must.” This is also why we’re seeing trends such as “shift left” start to fade in favor of emerging cybersecurity categories, like Application Detection & Response (ADR), but that’s another topic.
Some may not be familiar with Cyber Scene Investigation, but Binalyze describes its ability to facilitate incident response as:
“Allowing the organization to triage attacks, isolate compromised assets, and report accurately to stakeholders such as the board, regulators, and insurers.”
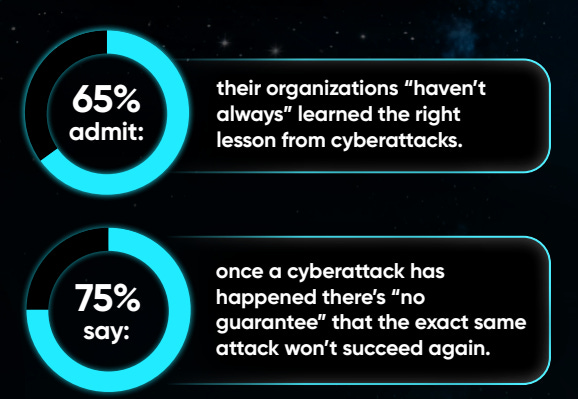
As we discussed above in the key findings, more than half of the CISOs in the report stated that they’re prone to falling victim to the same attack and aren’t learning from these lessons or implementing mitigating controls accordingly, leaving the organization exposed to subsequent incidents and risks.
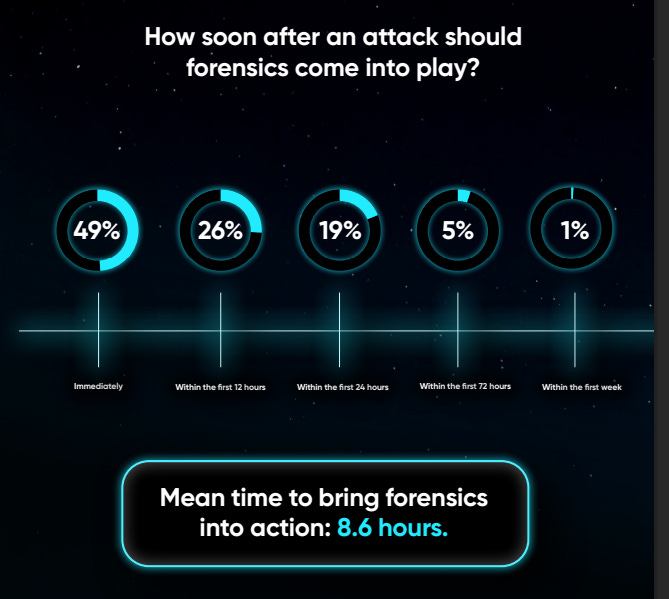
While roughly half of the CISOs agree that digital forensics should be involved immediately following the detection of an incident, the reality is much bleaker, with a mean time of 8.6 hours for forensics to get involved. Anyone who follows modern cyber trends knows that there is more than enough time for attackers to move laterally, embed themselves, exfiltrate sensitive data, and perform other malicious activities.
Here, we have a clear disconnect between what organizational security leaders think is optimal and the actual state of practice. Binalyze’s report also highlights the value that forensics can play proactively, not just being utilized post-incident or breach, but proactively facilitating activities such as threat hunting and vulnerability discovery.
(In)Effective Crisis Management
In the key takeaways, we also discussed how CISOs cited significant gaps and challenges with their crisis management. This is evident in the fact that less than half of the CISOs surveyed have confidence in their organization’s crisis management framework.
This aligns with the technical capability gaps we discussed previously, with organizations disproportionately investing in prevention tools and techniques, but not equally in their ability to respond to incidents when they occur.
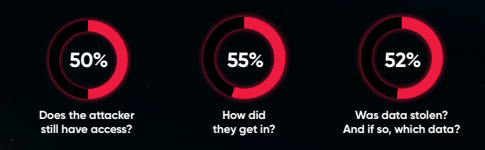
Binalyze highlights key questions security leaders need to be capable of answering, such as:
Does the attacker still have access?
How did they get in?
Was data stolen, and if so, what data?
Any security practitioner knows that these are fundamental questions, important not just for cyber and risk management activities, but also crucial regarding incident and customer disclosures, regulatory requirements, and more.
But, as the Binalyze report demonstrates, only roughly half of the CISOs they spoke to were confident they could answer these questions effectively:
So not only are organizations struggling to prevent incidents despite prioritized investments, when one does occur, they’re essentially blind to understanding its scope, scale, and impact, all of which are crucial for being able to respond and recover, key aspects of leading frameworks, such as the NIST Cybersecurity Framework (CSF).
This lack of visibility and context also manifests in the report, with an astounding 64% of attacks not being acted upon by CISOs; nearly half of attacks go completely undetected, and even identified attacks or suspicious activity are not addressed.
This is likely why organizations often discover incidents through external sources and third parties, due to gaps in their internal capabilities for detection and response. This also hinders their ability to share threat intelligence and related information with peer organizations that may fall victim to similar attacks.
How often have we heard “CISOs need to speak the language of the business”? Yet, with these glaring gaps in detection and response, CISOs and security leaders are ill-prepared to brief critical stakeholders, such as the board, about the details of a breach. This is a problem, as this undermines the CISO's credibility with business peers and could even put the security leader's job in jeopardy if they’re viewed as ineffective and unable to answer basic questions about cyber incidents and their respective organizational impacts.
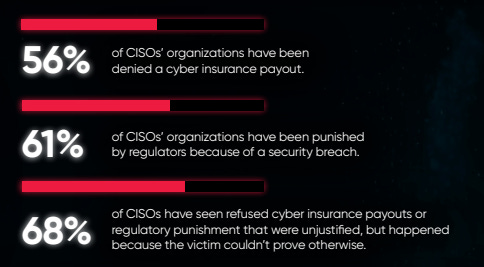
It’s not just the board or business peers where the struggles may have an impact, either. Binalyze’s report and insights from CISOs highlight real-world consequences, including denial of cyber insurance payouts or regulatory penalties.
I mentioned above how the average cyberattack investigation wasn’t occurring until 8.5 days post-incident, and those delays are having real financial consequences for organizations, reaffirming the negative reputation cybersecurity has as a cost center.
This is pretty damning from a security perspective, as not only are we costing the business in terms of developmental delays to implement security, costs to establish security programs and tech stacks, but then when incidents do occur, the very thing security is here to address, delays in investigation and responses are costing the organization hundreds of thousands to millions in additional costs due to our ineffective detection and response capabilities.
Binalyze’s report goes on to identify specifics regarding the lack of insights and visibility:
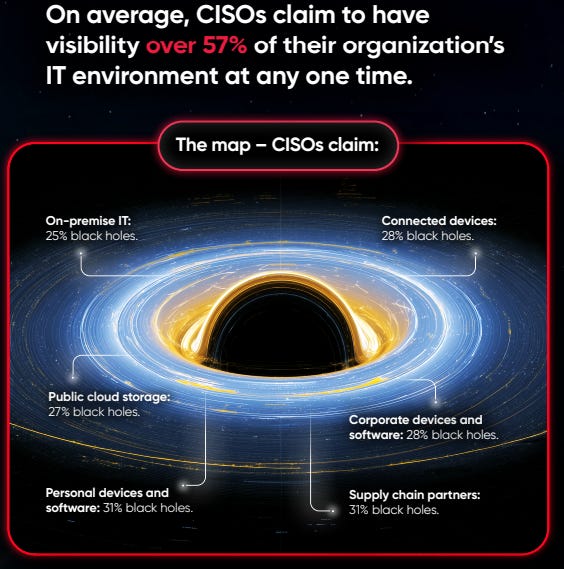
This highlights that most CISOs know they’re missing key information during breaches, start without sufficient information, and know their investigations are incomplete even when they “finish” them. What’s notable is that longstanding leading cyber control sources, such as the CIS Critical Security Controls, consistently rank asset inventory as a top control.
As the saying goes, you cannot protect what you don’t know exists.
Yet, Binalyze’s report and insights from the CISOs show that most acknowledge they only have visibility over half of their enterprises and have critical visibility gaps spanning key areas such as on-prem, cloud, endpoints, BYoD, and supply chains.
I’ve written about cybersecurity tool sprawl many times, noting that it can even make organizations less secure, as the security tools overwhelm the security team, leading to cognitive overload, burnout, and fatigue.
They also become shelfware, with many security tools never being fully configured, tuned, or optimized, leading to them not providing ROI and not reducing organizational risks. Worse yet, they often lead to even more risks, as attackers routinely target security products, knowing they have elevated privileges and access to sensitive data, which is often not monitored, and frequently share the same software flaws as broader software products.
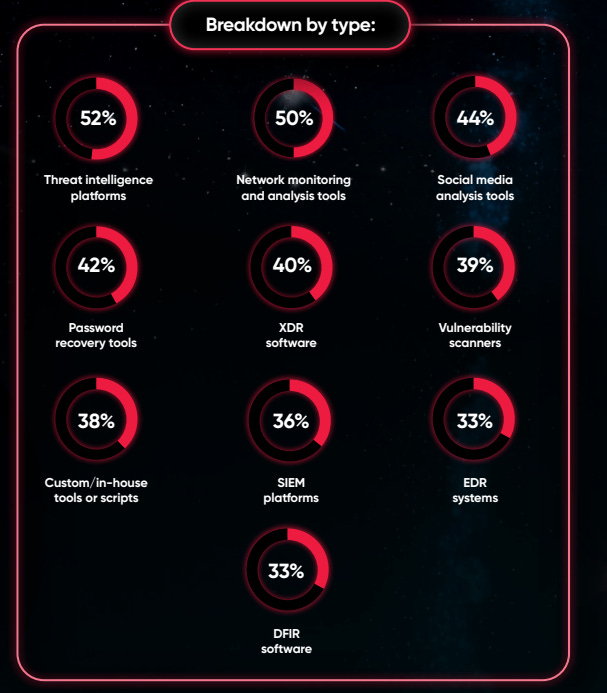
This problem is pervasive in the cyber investigation space, with the Binalyze report finding that enterprises, on average, have 11 tools to investigate cyberattacks.
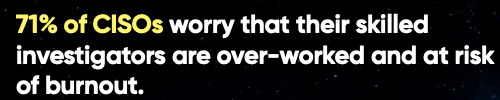
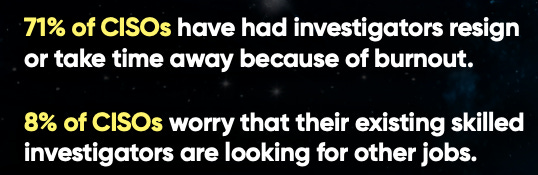
This burnout is seen in the report too, with most CISOs citing concerns about their staff being overworked.
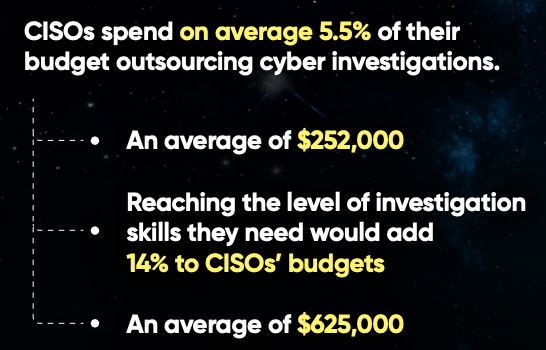
Despite concerns about burnout and fears of attrition, less than half of the CISOs surveyed stated they had the in-house skills needed to effectively perform investigations, leading to significant outsourcing costs, as shown below.
CISOs often opt for outsourcing, recognizing that they are unlikely to receive the budgetary boosts necessary to bring investigations fully in-house, and it is more cost-effective to engage a third-party.
All is not lost, though, as modern, innovative detection platforms and capabilities can address some of the systemic visibility challenges, while also augmenting and amplifying internal expertise and teams.
This can address the gaps in CISOs’ crisis management abilities, as well as slash the long timelines associated with kicking off and effectively carrying out forensic investigations, and even pivot from a reactive to proactive approach, leveraging deep visibility and context to address the challenges and mitigate the risk and financial impacts to their organizations.
I discussed many of these concepts previously, with Emre Tinaztepe of the Binalyze team, in an episode of Resilient Cyber titled “Forensics at the Frontline: Powering AI and Automation in the SOC”.
During that discussion, we explored the excitement surrounding AI for security, including SecOps and the SOC, and how AI can be leveraged to accelerate and enhance incident response. We walked through how teams can couple digital forensics with live incident response workflows to mitigate the impact of incidents and improve security outcomes, including key metrics such as MTTD/MTTR.
You can catch that full conversation below:
Closing Thoughts
In an era where cybersecurity budget growth is slowing as well as facing increased scrutiny around ROI, Binalyze’s 2025 State of Cybersecurity Investigations Report sheds critical light on a problem that is pervading the ecosystem, and leading to significant costs to organizations as well as increased risks. Inefficiencies and systemic challenges in SecOps and investigation capabilities are further exposing organizations to cybersecurity risks as well as impeding their ability to recover, when those risks materialize.
But, the opportunity to address these deep rooted problems is there, if we’re willing to confront the gaps and take a new approach!